Manual
Table Of Contents
- 1. INTRODUTION
- 2. INSTALLATION
- 3. SWITCH MANAGEMENT
- 4. WEB CONFIGURATION
- 4.1 Main WEB PAGE
- 4.2 System
- 4.3 Simple Network Management Protocol
- 4.4 Port Management
- 4.5 Link Aggregation
- 4.6 VLAN
- 4.7 Rapid Spanning Tree Protocol
- 4.8 Quality of Service
- 4.9 Multicast
- 4.10 IEEE 802.1X Network Access Control
- 4.10.1 Understanding IEEE 802.1X Port-Based Authentication
- 4.10.2 802.1X System Configuration
- 4.10.3 802.1X and MAC-Based Authentication Port Configuration
- 4.10.4 802.1X Port Status
- 4.10.5 802.1X and MAC-Based Authentication Statistics
- 4.10.6 Windows Platform RADIUS Server Configuration
- 4.10.7 802.1X Client Configuration
- 4.11 Access Control Lists
- 4.12 Address Table
- 4.13 Port Security (To be Continued)
- 4.14 LLDP
- 4.15 Network Diagnastics
- 4.16 Stacking – SGSW-24040 / SGSW-24040R
- 4.17 Power over Ethernet (SGSW-24040P / SGSW-24040P4)
- 5. COMMAND LINE INTERFACE
- 6. Command Line Mode
- 6.1 System Command
- 6.2 Port Management Command
- 6.3 Link Aggregation Command
- 6.4 VLAN Configuration Command
- 6.5 Spanning Tree Protocol Command
- 6.6 Multicast Configuration Command
- 6.7 Quality of Service Command
- 6.8 802.1x Port Access Control Command
- 6.9 Access Control List Command
- 6.10 MAC Address Table Command
- 6.11 LLDP Command
- 6.12 Stack Management Command
- 6.13 Power over Ethernet Command
- 7. SWITCH OPERATION
- 8. POWER OVER ETHERNET OVERVIEW
- 9. TROUBLE SHOOTING
- APPENDEX A
- APPENDEX B : GLOSSARY
User’s Manual of WGSW-24040 Series
SGSW-24040/24240 Series
162
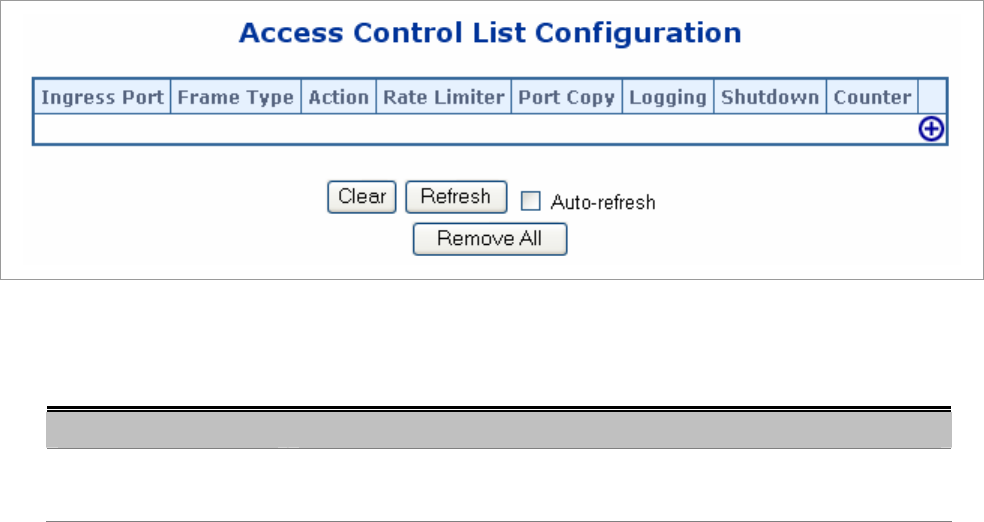
4.11 Access Control Lists
ACL is an acronym for Access Control List. It is the list table of ACEs, containing access control entries that specify individual
users or groups permitted or denied to specific traffic objects, such as a process or a program.
Each accessible traffic object contains an identifier to its ACL. The privileges determine whether there are specific traffic object
access rights.
ACL implementations can be quite complex, for example, when the ACEs are prioritized for the various situation. In networking,
the ACL refers to a list of service ports or network services that are available on a host or server, each with a list of hosts or
servers permitted or denied to use the service. ACL can generally be configured to control inbound traffic, and in this context,
they are similar to firewalls.
ACE is an acronym for Access Control Entry. It describes access permission associated with a particular ACE ID.
There are three ACE frame types (Ethernet Type, ARP, and IPv4) and two ACE actions (permit and deny). The ACE also
contains many detailed, different parameter options that are available for individual application.
4.11.1 Access Control List Configuration
This page shows the Access Control List (ACL), which is made up of the ACEs defined for this Managed Switch. Each row
describes the ACE that is defined.
The maximum number of ACEs is 128.
Click on the lowest plus sign to add a new ACE to the list.
The Access Control List Configuration screen in Figure 4-11-1 appears.
Figure 4-11-1 Access Control List Configuration page screenshot
The page includes the following fields:
Object Description
• Ingress Port
Indicates the ingress port of the ACE. Possible values are:
• Any: The ACE will match any ingress port.










