User's Manual
Table Of Contents
- ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
- Contents
- About This Manual
- Chapter 1 Introduction
- Chapter 2 Using the Setup Wizard to Provision the STM in Your Network
- Choosing a Deployment Scenario
- Understanding the Steps for Initial Connection
- Logging In to the STM
- Using the Setup Wizard to Perform the Initial Configuration
- Setup Wizard Step 1 of 10: Introduction
- Setup Wizard Step 2 of 11: Networking Settings
- Setup Wizard Step 3 of 11: Time Zone
- Setup Wizard Step 4 of 11: Email Security
- Setup Wizard Step 5 of 11: Web Security
- Setup Wizard Step 6 of 11: Email Notification Server Settings
- Setup Wizard Step 7 of 11: Update Settings
- Setup Wizard Step 8 of 11: HTTP Proxy Settings
- Setup Wizard Step 9 of 11: Web Categories
- Setup Wizard Step 10 of 11: Configuration Summary
- Setup Wizard Step 11 of 11: Restarting the System
- Verifying Proper Installation
- Registering the STM with NETGEAR
- What to Do Next
- Chapter 3 Performing Network and System Management
- Configuring Network Settings
- Configuring Session Limits and Timeouts
- Configuring the HTTP Proxy Settings
- About Users with Administrative and Guest Privileges
- Configuring Remote Management Access
- Using an SNMP Manager
- Managing the Configuration File
- Updating the Software
- Configuring Date and Time Service
- Managing Digital Certificates
- Managing the Quarantine Settings
- Performance Management
- Chapter 4 Content Filtering and Optimizing Scans
- About Content Filtering and Scans
- Configuring E-mail Protection
- Configuring Web and Services Protection
- Configuring Application Control
- Setting Scanning Exclusions and Web Access Exceptions
- Chapter 5 Managing Users, Groups, and Authentication
- About Users, Groups, and Domains
- Configuring Groups
- Configuring User Accounts
- Configuring Authentication
- Global User Settings
- Viewing and Logging Out Active Users
- Chapter 6 Monitoring System Access and Performance
- Chapter 7 Troubleshooting and Using Online Support
- Appendix A Default Settings and Technical Specifications
- Appendix B Related Documents
- Index
ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
Performing Network and System Management 3-25
v1.0, September 2009
Managing Digital Certificates
The STM uses digital certificates (also known as X509 certificates) for secure web access
connections over HTTPS (that is, SSL VPN connections).
Digital certificates can be either self-signed or can be issued by certification authorities (CAs) such
as an internal Windows server or an external organizations such as Verisign or Thawte. On the
STM, the uploaded digital certificate is checked for validity and purpose. The digital certificate is
accepted when it passes the validity test and the purpose matches its use.
The STM uses digital certificates to authenticate connecting HTTPS servers, and to allow HTTPS
clients to be authenticated by remote entities. A digital certificate that authenticates a server, for
example, is a file that contains the following elements:
• A public encryption key to be used by clients for encrypting messages to the server.
• Information identifying the operator of the server.
• A digital signature confirming the identity of the operator of the server. Ideally, the signature is
from a trusted third party whose identity can be verified.
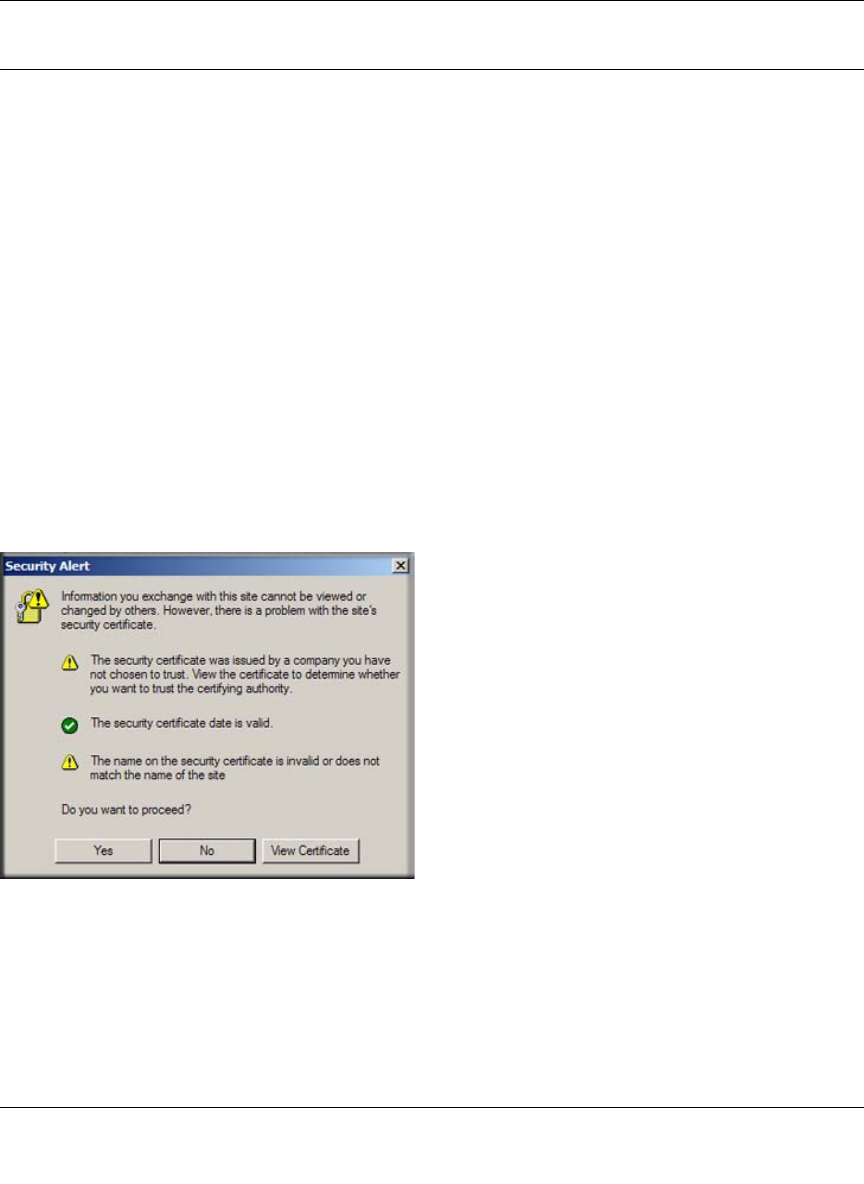
When a security alert is generated, the user can decide whether or not to trust the host.
You can obtain a digital certificate from a well-known commercial certificate authority (CA) such
as Verisign or Thawte. Because a commercial CA takes steps to verify the identity of an applicant,
a digital certificate from a commercial CA provides a strong assurance of the server’s identity.
The STM contains a self-signed digital certificate from NETGEAR. This certificate can be
downloaded from the STM login screen or from the Certificate Management screen for browser
Figure 3-14










