User's Manual
Table Of Contents
- ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
- Contents
- About This Manual
- Chapter 1 Introduction
- Chapter 2 Using the Setup Wizard to Provision the STM in Your Network
- Choosing a Deployment Scenario
- Understanding the Steps for Initial Connection
- Logging In to the STM
- Using the Setup Wizard to Perform the Initial Configuration
- Setup Wizard Step 1 of 10: Introduction
- Setup Wizard Step 2 of 11: Networking Settings
- Setup Wizard Step 3 of 11: Time Zone
- Setup Wizard Step 4 of 11: Email Security
- Setup Wizard Step 5 of 11: Web Security
- Setup Wizard Step 6 of 11: Email Notification Server Settings
- Setup Wizard Step 7 of 11: Update Settings
- Setup Wizard Step 8 of 11: HTTP Proxy Settings
- Setup Wizard Step 9 of 11: Web Categories
- Setup Wizard Step 10 of 11: Configuration Summary
- Setup Wizard Step 11 of 11: Restarting the System
- Verifying Proper Installation
- Registering the STM with NETGEAR
- What to Do Next
- Chapter 3 Performing Network and System Management
- Configuring Network Settings
- Configuring Session Limits and Timeouts
- Configuring the HTTP Proxy Settings
- About Users with Administrative and Guest Privileges
- Configuring Remote Management Access
- Using an SNMP Manager
- Managing the Configuration File
- Updating the Software
- Configuring Date and Time Service
- Managing Digital Certificates
- Managing the Quarantine Settings
- Performance Management
- Chapter 4 Content Filtering and Optimizing Scans
- About Content Filtering and Scans
- Configuring E-mail Protection
- Configuring Web and Services Protection
- Configuring Application Control
- Setting Scanning Exclusions and Web Access Exceptions
- Chapter 5 Managing Users, Groups, and Authentication
- About Users, Groups, and Domains
- Configuring Groups
- Configuring User Accounts
- Configuring Authentication
- Global User Settings
- Viewing and Logging Out Active Users
- Chapter 6 Monitoring System Access and Performance
- Chapter 7 Troubleshooting and Using Online Support
- Appendix A Default Settings and Technical Specifications
- Appendix B Related Documents
- Index
ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
6-38 Monitoring System Access and Performance
v1.0, September 2009
• Send as Ham. The selected spam e-mail files are not tagged as spam for Distributed Spam
Analysis, are deleted from the quarantine file, and are sent to the intended recipients.
• Delete. The selected spam e-mail files are deleted from the quarantine file.
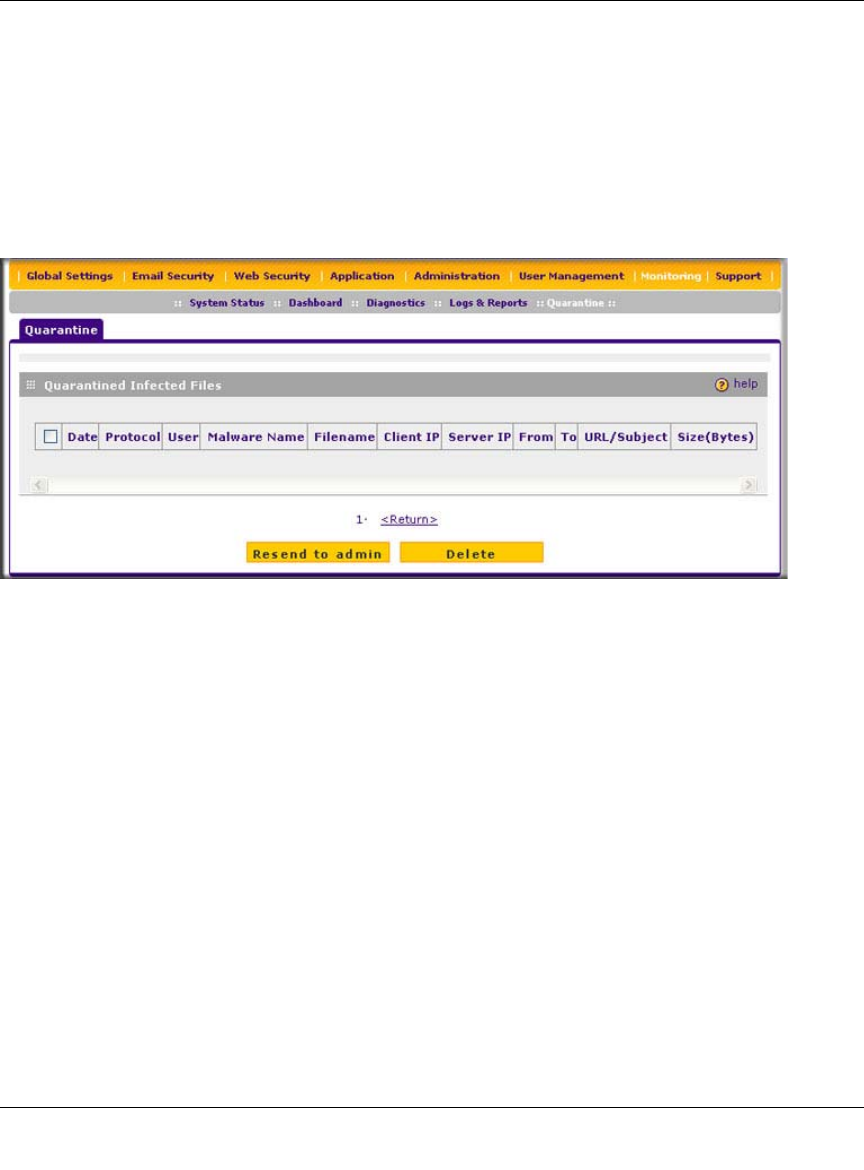
Viewing and Managing the Quarantined Infected Files Table
When you query the malware quarantine file, the Quarantine screen with the Quarantined Infected
Files table displays (see Figure 6-17).
The Quarantined Infected Files table shows the following columns:
• Checkbox. Lets you select the table entry.
• Date. The date that the file was received.
• Protocol. The protocol (SMTP, POP3, IMAP, HTTP, FTP, HTTPS) in which the spyware or
virus was found.
• User. The user name that was used to log on the STM.
• Malware name. The name of the spyware or virus.
• File name. The name of the file in which the spyware or virus was found.
• Client IP. The client IP address from which the spyware or virus originated.
• Server IP. The server IP address from which the spyware or virus originated.
• From. The e-mail address of the sender.
• To. The e-mail address of the recipient.
• URL/Subject. The URL or subject that is associated with the spyware or virus.
• Size (Bytes). The size of the virus or spyware file in bytes.
Figure 6-17










