User's Manual
Table Of Contents
- ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
- Contents
- About This Manual
- Chapter 1 Introduction
- Chapter 2 Using the Setup Wizard to Provision the STM in Your Network
- Choosing a Deployment Scenario
- Understanding the Steps for Initial Connection
- Logging In to the STM
- Using the Setup Wizard to Perform the Initial Configuration
- Setup Wizard Step 1 of 10: Introduction
- Setup Wizard Step 2 of 11: Networking Settings
- Setup Wizard Step 3 of 11: Time Zone
- Setup Wizard Step 4 of 11: Email Security
- Setup Wizard Step 5 of 11: Web Security
- Setup Wizard Step 6 of 11: Email Notification Server Settings
- Setup Wizard Step 7 of 11: Update Settings
- Setup Wizard Step 8 of 11: HTTP Proxy Settings
- Setup Wizard Step 9 of 11: Web Categories
- Setup Wizard Step 10 of 11: Configuration Summary
- Setup Wizard Step 11 of 11: Restarting the System
- Verifying Proper Installation
- Registering the STM with NETGEAR
- What to Do Next
- Chapter 3 Performing Network and System Management
- Configuring Network Settings
- Configuring Session Limits and Timeouts
- Configuring the HTTP Proxy Settings
- About Users with Administrative and Guest Privileges
- Configuring Remote Management Access
- Using an SNMP Manager
- Managing the Configuration File
- Updating the Software
- Configuring Date and Time Service
- Managing Digital Certificates
- Managing the Quarantine Settings
- Performance Management
- Chapter 4 Content Filtering and Optimizing Scans
- About Content Filtering and Scans
- Configuring E-mail Protection
- Configuring Web and Services Protection
- Configuring Application Control
- Setting Scanning Exclusions and Web Access Exceptions
- Chapter 5 Managing Users, Groups, and Authentication
- About Users, Groups, and Domains
- Configuring Groups
- Configuring User Accounts
- Configuring Authentication
- Global User Settings
- Viewing and Logging Out Active Users
- Chapter 6 Monitoring System Access and Performance
- Chapter 7 Troubleshooting and Using Online Support
- Appendix A Default Settings and Technical Specifications
- Appendix B Related Documents
- Index
ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
Content Filtering and Optimizing Scans 4-41
v1.0, September 2009
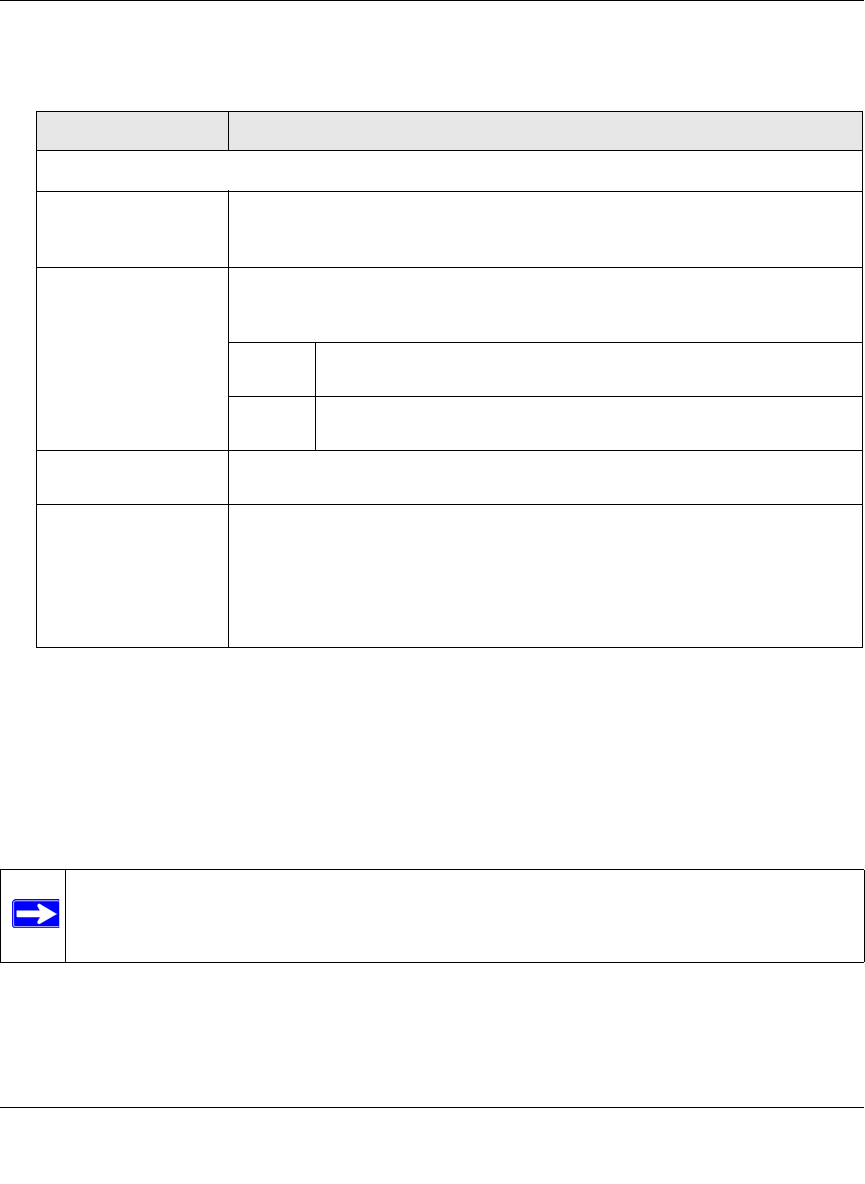
3. Complete the fields and select the checkbox as explained in Table 4-14.
4. Click Apply to save your settings.
Configuring FTP Scans
Some malware threats are specifically developed to spread through the FTP protocol. By default,
the STM scans FTP traffic, but you can specify how the STM scans FTP traffic and which action is
taken when a malware threat is detected.
To configure the FTP scan settings:
1. Select Web Security > FTP from the menu. The FTP screen displays (see Figure 4-19 on
page 4-42).
Table 4-14. Trusted Hosts Settings
Setting Description
Do Not Intercept HTTPS Connections for the following Hosts
Enable Select this checkbox to bypass scanning of trusted hosts that are listed in the
Hosts field. Users do not receive a security alert for trusted hosts that are listed
in the Host field.
Hosts This field contains the trusted hosts for which scanning is bypassed. To add a
host to this field, use the Add Host field or the Import from File tool (see below).
You can add a maximum of 200 URLs.
delete To delete one or more hosts, highlight the hosts, and click the
delete table button.
export To export the hosts, click the export table button and follow the
instructions of your browser.
Add Host Type or copy a trusted host in the Add Host field. Then, click the add table
button to add the host to the Host field.
Import from File To import a list with trusted hosts into the Host field, click the Browse button
and navigate to a file in .txt format that contains line-delimited hosts (that is,
one host per line). Then, click the upload table button to add the hosts to the
Host field.
Note: Any existing hosts in the Host field are overwritten when you import a list
of hosts from a file.
Note: The STM does not scan password-protected FTP files.










