HP XP P9000 Provisioning for Mainframe Systems User Guide
Table Of Contents
- HP XP P9000 Provisioning for Mainframe Systems User Guide
- Contents
- 1 Introduction to provisioning
- About provisioning
- Basic provisioning
- Fixed-sized provisioning
- Disadvantages
- When to use fixed-sized provisioning
- Custom-sized provisioning
- When to use custom-sized provisioning
- Basic provisioning workflow
- Thin Provisioning Overview
- Thin Provisioning Z
- Thin Provisioning Z concepts
- When to use Thin Provisioning Z
- Thin Provisioning Z advantages
- Thin Provisioning Z advantage example
- Thin Provisioning Z work flow
- Smart Tiers Z
- Tiers concept
- When to use Smart Tiers Z
- Resource groups strategies
- Complimentary strategies
- Key terms
- Before you begin
- About pool volumes
- 2 Configuring resource groups
- System configuration using resource groups
- Resource groups examples
- Meta_resource
- Resource lock
- User groups
- Resource group assignments
- Resource group license requirements
- Resource group rules, restrictions, and guidelines
- Creating a resource group
- Adding resources to a resource group
- Removing resources from a resource group
- Managing Resource Groups
- Using Resource Partition and other P9500 products
- 3 Configuring custom-sized provisioning
- Virtual LVI/Virtual LUN functions
- VLL requirements
- VLL specifications
- SSID requirements
- VLL size calculations
- Create LDEV function
- Blocking an LDEV
- Restoring a blocked LDEV
- Editing an LDEV name
- Deleting an LDEV (converting to free space)
- Formatting LDEVs
- Making external mainframe system volumes usable
- Assigning a processor blade
- Using a system disk
- 4 Configuring thin provisioning
- Thin Provisioning Z overview
- Smart Tiers Z overview
- Thin provisioning requirements
- Using Thin Provisioning Z or Smart Tiers Z with other P9500 products
- Thin Provisioning Z workflow
- Smart Tiers Z
- About tiered storage
- Tier monitoring and data relocation
- Smart Pool
- Tier monitoring and relocation cycles
- Tier relocation flow
- Tier relocation rules, restrictions, and guidelines
- Buffer area of a tier
- Smart Tiers Z cache specifications and requirements
- Execution modes for tier relocation
- Monitoring modes
- Notes on performing monitoring
- Downloading the tier relocation log file
- Tiering policy
- Tiering policy expansion
- Tiering policy examples
- Setting tiering policy on a THP V-VOL
- Tiering policy levels
- Viewing the tiering policy in the performance graph
- Reserving tier capacity when setting a tiering policy
- Example of reserving tier capacity
- Notes on tiering policy settings
- New page assignment tier
- Relocation priority
- Assignment tier when pool-VOLs are deleted
- Formatted pool capacity
- Rebalancing the usage level among pool-VOLs
- Execution mode settings and tiering policy
- Changing the tiering policy level on a THP V-VOL
- Changing new page assignment tier of a V-VOL
- Opening the Edit Tiering Policies window
- Changing a tiering policy
- Changing relocation priority setting of a V-VOL
- Smart Tiers Z workflow
- Smart Tiers Z tasks and parameters
- Managing Smart Tiers Z
- Changing a pool for Smart Tiers Z to a pool for Thin Provisioning Z
- Working with pools
- Working with THP V-VOLs
- Thresholds
- Working with SIMs
- Managing pools and THP V-VOLs
- Viewing pool information
- Viewing formatted pool capacity
- Viewing the progress of rebalancing the usage level among pool-VOLs
- Increasing pool capacity
- Changing a pool name
- Recovering a blocked pool
- Decrease pool capacity
- Deleting a tier in a pool
- Deleting a pool
- Changing external LDEV tier rank
- Increasing THP V-VOL capacity
- Changing the name of a THP V-VOL
- About releasing pages in a THP V-VOL
- Enabling/disabling tier relocation of a THP V-VOL
- Deleting a THP V-VOL
- 5 Configuring access attributes
- 6 Protecting volumes from I/O operations
- Overview of Volume Security for Mainframe
- Volume Security for Mainframe Requirements
- Volume Security for Mainframe Functions
- Protecting Volumes from I/O Operations at Mainframe Hosts
- Warnings Regarding Volume Security for Mainframe
- Supported Volume Emulation Types
- Maximum Number of Groups
- Maximum Number of Hosts and Volumes
- Launching Volume Security for Mainframe
- Viewing Security Settings
- Locating Volumes in a Specified Security Group
- Locating Security Groups that Contain a Specified Host
- Locating Volumes in a Security Group that Contains a Specified Host
- Locating Ports through Which Hosts Can Access Volumes
- Locating Security Groups that Contain a Specified Volume
- Locating Hosts in a Security Group that Contains a Specified Volume
- Locating Security Groups that Contain a Specified Host Group
- Locating Security Groups that Contain a Specified LDEV Group
- Limiting Host Access
- Prohibiting Host Access
- Protecting Volumes from Copy Operations
- Disabling Volume Security for Mainframe
- Editing Security Groups
- Editing Host Groups
- Editing LDEV Groups
- 7 Troubleshooting
- 8 Support and other resources
- A RAID Manager command reference
- B Resource Partition GUI reference
- C LDEV GUI reference
- Parity Groups window
- Parity Groups window after selecting Internal (or External) under Parity Groups
- Window after selecting a parity group under Internal (or External) of Parity Groups
- Window after selecting Logical Devices
- Create LDEVs wizard
- Edit LDEVs wizard
- Change LDEV Settings window
- View SSIDs window
- Select Free Spaces window
- Select Pool window
- View LDEV IDs window
- View Physical Location window
- Edit SSIDs window
- Change SSIDs window
- Format LDEVs wizard
- Restore LDEVs window
- Block LDEVs window
- Delete LDEVs window
- LDEV Properties window
- Top window when selecting Components
- Top window when selecting controller chassis under Components
- Edit Processor Blades wizard
- Assign Processor Blade wizard
- View Management Resource Usage window
- D Thin Provisioning Z and Smart Tiers Z GUI reference
- Pools window after selecting pool (Pools window)
- Top window when selecting a pool under Pools
- Create Pools wizard
- Expand Pool wizard
- Edit Pools wizard
- Delete Pools wizard
- Expand V-VOLs wizard
- Restore Pools window
- Shrink Pool window
- Stop Shrinking Pools window
- Complete SIMs window
- Select Pool VOLs window
- Reclaim Zero Pages window
- Stop Reclaiming Zero Pages window
- Pool Property window
- View Tier Properties window
- Monitor Pools window
- Stop Monitoring Pools window
- Start Tier Relocation window
- Stop Tier Relocation window
- View Pool Management Status window
- Edit External LDEV Tier Rank wizard
- Edit Tiering Policies wizard
- Change Tiering Policy Window
- E Volume Retention GUI reference
- F Volume Security for Mainframe GUI reference
- Volume Security for Mainframe window
- Add/Change Security Group Dialog Box
- Add/Change Host Group Dialog Box
- Add/Change LDEV Group Dialog Box
- Select LDEV Dialog Box
- Select Port Dialog Box
- Specify Security Group Dialog Box
- Host to Security Group Dialog Box
- Host to LDEV Dialog Box
- Host Group to Security Group Dialog Box
- Host Group to Port Dialog Box
- LDEV to Security Group Dialog Box
- LDEV to Host Dialog Box
- LDEV Group to Security Group Dialog Box
- Error Detail Dialog Box
- Glossary
- Index
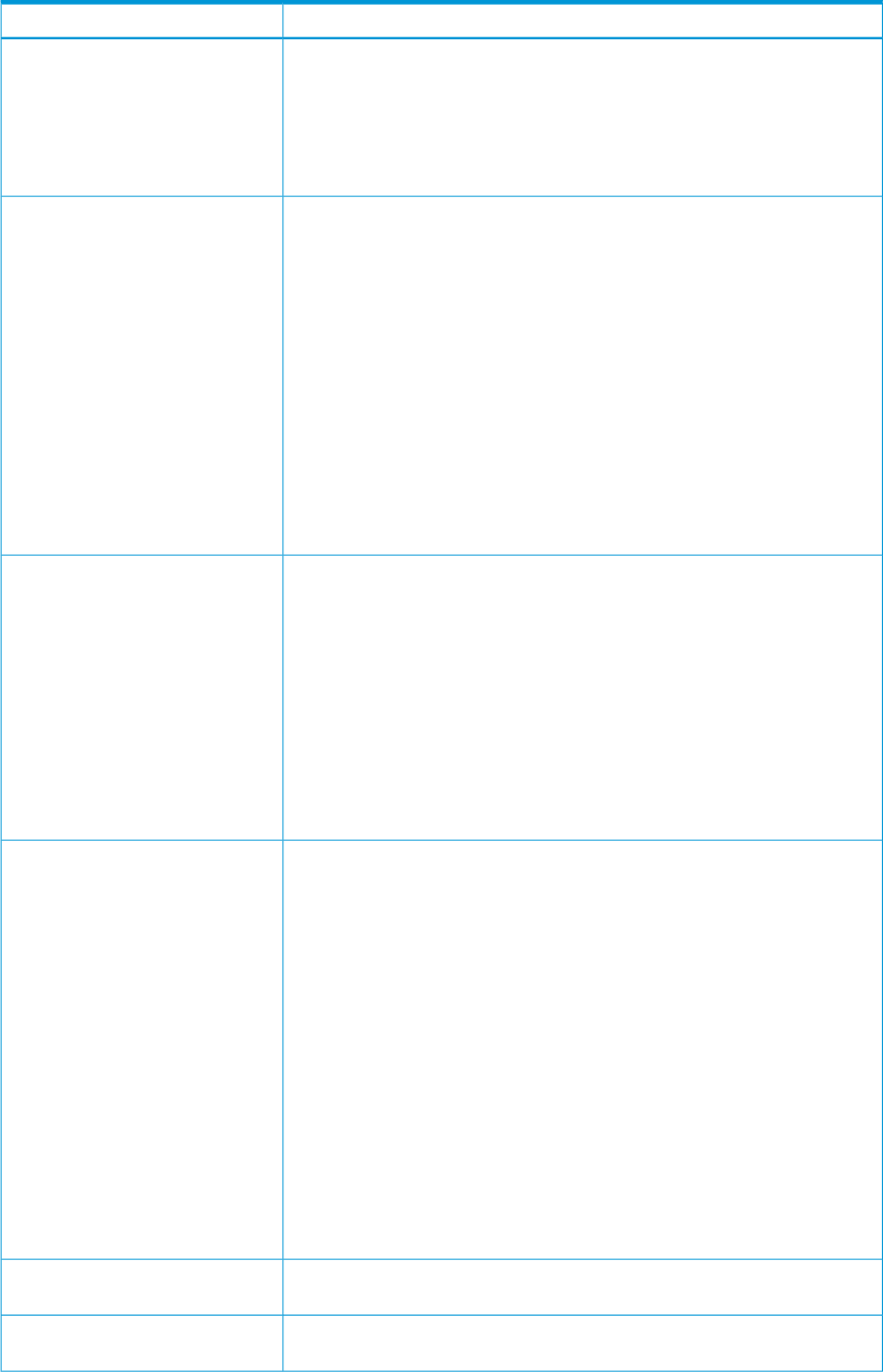
DescriptionItem
The following conventions apply to security group names:
• Up to eight characters can be used in a name.
• Characters are case-sensitive.
• The following characters cannot be used: \ , / : ; * ? " < > |.
• A space cannot be used as the first or last character of a name.
Specify no change, enable, or disable for security settings. The default is Enable.Security
• No Change does not change the security status of the security groups selected
in the Security Group List table. For example, if you select a security-enabled
group and a security-disabled group in the table, Disable disables security
settings in both groups, but No Change does not change the current security
status for either group (the former remains security-enabled and the latter
remains security-disabled).
• Enable enables the security settings that are made in the security groups
selected in the Security Groups table.
Caution: It is possible that security settings are disabled even when Enable
is selected. If Access is selected in the Group Status box (see below) and the
security group does not contain a host group or an LDEV group, security
settings are disabled unconditionally in the security group.
• Disable disables the security settings that are made in the security groups
selected in the Security Groups table.
Sets a selected security group as an access group or pool group. The default is
Access.
Group Status
• No Change prevents a change in the group status of the security groups
selected in the Security Group List table. For example, if you select one access
group and one pool group, Access changes the two groups into access groups,
but No Change does not change the two groups. The former remains an
access group and the latter remains a pool group.
• Access specifies the selected security groups as access groups. Volumes in
access groups can be accessed only by hosts registered in the same access
group and cannot be accessed by other hosts.
• Pool specifies the selected security groups as pool groups. Volumes in pool
groups cannot be accessed by any hosts.
Specifies whether volumes in the security group can be used as secondary
volumes (copy destination volumes). The default is Enable.
T-VOL/S-VOL
• No Change does not change the secondary volume settings of the security
groups selected in the Security Group List table. For example, if volumes in
one of the selected security groups are usable as copy destinations, but
volumes in the other security group are unusable, Enable makes volumes in
both groups usable as destinations. However, No Change does not change
volumes in either groups. The former remains usable, and the latter remains
unusable.
• Enable makes volumes in the selected security groups usable as secondary
volumes (copy destinations).
• Disable makes volumes in the selected security groups unusable as secondary
volumes (copy destinations).
Note: Secondary volumes (copy destination volumes) are often referred to as
remote volumes or R-VOLs in the P9000 Continuous Access Synchronous for
Mainframe Systems User Guide. Secondary volumes are referred to as target
volumes or T-VOLs in the P9000 Business Copy for Mainframe Systems User
Guide.
Enter the name of a new security group and click Add to add the new security
group to the Security Group List table.
Add
When settings of the selected security groups are changed, click Change to make
the changes appear in the Security Group List table.
Change
312 Volume Security for Mainframe GUI reference










