HP-UX Reference (11i v2 04/09) - 1 User Commands A-M (vol 1)
c
chatr_pa(1) chatr_pa(1)
(For PA-RISC Systems)
executing code on their stack(s). Ideally this option should be set (if needed) by the program’s provider, to
minimize the need for manual intervention by whomever installs the program.
An alternate method is setting the kernel tunable parameter,
executable_stack
, to set a system-
wide default for whether stacks are executable. Setting the
executable_stack
parameter to 1 (one)
with
sam (see sam(1M)) tells the HP-UX kernel not to execute protect program stack(s). This is the pre-
ferred setting if compatibility with older releases is more important than security. Setting it to a 0 (zero)
is appropriate if security is more important than compatibility. This is the recommended setting, because
it significantly improves system security with minimal, if any, negative effects on legitimate applications.
Combinations of these settings may be appropriate for many applications. For example, after setting
executable_stack
to 0, you may find that one or two critical applications no longer work because
they have a legitimate need to execute from their stack(s). Programs such as simulators or interpreters
that use self-modifying code are examples you might encounter. To obtain the security benefits of a res-
trictive system default while still letting these specific applications run correctly, set
executable_stack
to 0, and run chatr +es enable on the specific binaries that need to execute
code from their stack(s). These binaries can be easily identified when they are executed, because they
will print error messages referring to this manual page.
The possible settings for
executable_stack
are as follows:
executable_stack
= 0 (default)
A setting of 0 (the default value) causes stacks to be non-executable and is strongly preferred
from a security perspective.
executable_stack
= 1
A setting of 1 causes all program stacks to be executable, and is safest from a compatibility
perspective but is the least secure setting for this parameter.
executable_stack =
2
A setting of 2 is equivalent to a setting of 0, except that it gives non-fatal warnings instead of
terminating a process that is trying to execute from its stack. Using this setting is helpful for
users to gain confidence that using a value of 0 will not hurt their legitimate applications.
Again, there is less security protection.
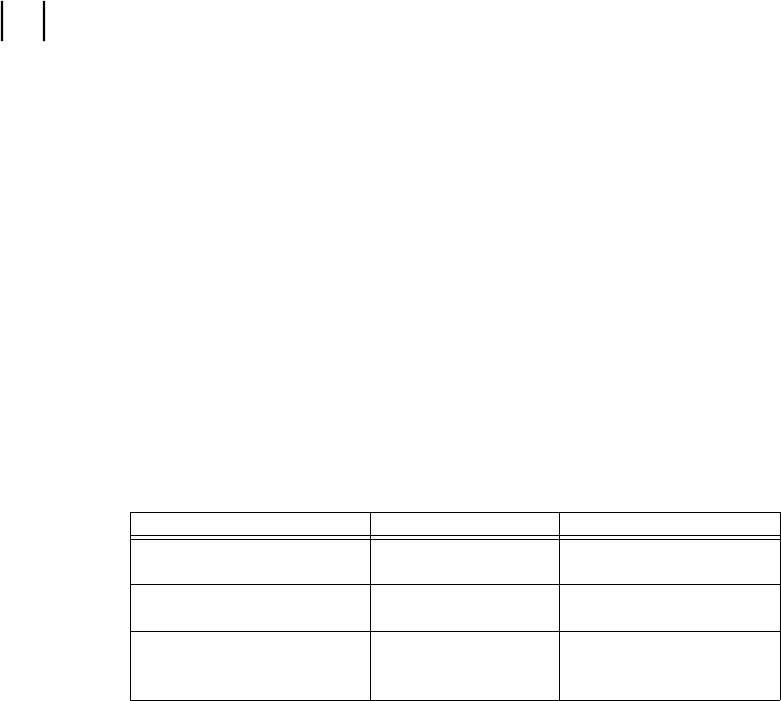
The table below summarizes the results from using the possible combinations of
chatr +es and
executable_stack when executing from the program’s stack. Running
chatr +es disable relies
solely on the setting of the
executable_stack
kernel tunable parameter when deciding whether or
not to grant execute permission for stacks and is equivalent to not having run
chatr +es on the binary.
chatr +es executable_stack ACTION
enable 1 program runs normally
disable or chatr is not run 1 program runs normally
enable 0 program runs normally
disable or chatr is not run 0 program is killed
enable 2 program runs normally
disable or chatr is not run 2 program runs normally
with warning displayed
RETURN VALUE
chatr returns zero on success. If the command line contents is syntactically incorrect, or one or more of
the specified files cannot be acted upon, chatr returns information about the files whose attributes could
not be modified. If no files are specified, chatr returns decimal 255.
Illegal options
For PA-RISC 32-bit
chatr, if you use an illegal option, chatr returns the number of words in the com-
mand line. For example,
chatr +b enable +xyz enable returns 5 (because of illegal option +xyz).
chatr +b enable +xyz enable +mno file1 file2 returns 8.
For PA-RISC 64-bit
chatr, if you use an illegal option, chatr returns the number of non-option words
present after the first illegal option.
chatr +b enable +xyz enable +mno enable +pqr enable file returns 4.
Section 1−−96 Hewlett-Packard Company − 5 − HP-UX 11i Version 2: September 2004










