LDAP-UX Client Services B.04.15 with Microsoft Windows Active Directory Server Administrator's Guide (edition 8)
Table Of Contents
- LDAP-UX Client Services B.04.15 with Microsoft Windows Active Directory Administrator's Guide
- Table of Contents
- Preface
- 1 Introduction
- 2 Installing LDAP-UX Client Services
- Before You Begin
- Summary of Installing and Configuring LDAP-UX Client Services
- Planning Your Installation
- Installing LDAP-UX Client Services on a Client
- Configuring Active Directory for HP-UX Integration
- Step 1: Install Active Directory
- Step 2: Install SFU 2.0, 3.0 or 3.5 including Server for NIS
- Step 3: Create a Proxy User
- Step 4: Add an HP-UX Client Machine Account to Active Directory
- Step 5: Use ktpass to Create the Keytab File for the HP-UX client machine
- Step 6: Add POSIX Attributes into the Global Catalog
- Importing Name Service Data into Your Directory
- Configuring LDAP-UX Client Services
- Step 1: Run the Setup Program
- Step 2: Install the PAM Kerberos Product
- Step 3: Configure Your HP-UX Machine to Authenticate Using PAM Kerberos
- Step 4: Configure the Name Service Switch (NSS)
- Step 5: Configure the PAM Authorization Service Module (pam_authz)
- Step 6: Configure the Disable Login Flag
- Step 7: Verify LDAP-UX Client Services for Single Domain
- Step 8: Configure Subsequent Client Systems
- Configuring the LDAP-UX Client Services with SSL or TLS Support
- Downloading the Profile Periodically
- 3 Active Directory Multiple Domains
- 4 LDAP-UX Client Services with AutoFS Support
- 5 LDAP Printer Configurator Support
- 6 Dynamic Group Support
- 7 Administering LDAP-UX Client Services
- Using the LDAP-UX Client Daemon
- Integrating with Trusted Mode
- SASL GSSAPI Support
- PAM_AUTHZ Login Authorization
- Policy And Access Rules
- How Login Authorization Works
- PAM_AUTHZ Supports Security Policy Enforcement
- Policy File
- Policy Validator
- Dynamic Variable Support
- Constructing an Access Rule in pam_authz.policy
- Static List Access Rule
- Dynamic Variable Access Rule
- Security Policy Enforcement with Secure Shell (SSH) or r-commands
- Adding Additional Domain Controllers
- Adding Users, Groups, and Hosts
- User and Group Management
- Displaying the Proxy User's Distinguished Name
- Verifying the Proxy User
- Creating a New Proxy User
- Displaying the Current Profile
- Creating a New Profile
- Modifying a Profile
- Changing Which Profile a Client is Using
- Creating an /etc/krb5.keytab File
- Considering Performance Impacts
- Client Daemon Performance
- Troubleshooting
- 8 Modifying User Information
- 9 Mozilla LDAP C SDK
- A Configuration Worksheet
- B LDAP-UX Client Services Object Classes
- C Command, Tool, Schema Extension Utility, and Migration Script Reference
- LDAP-UX Client Services Components
- Client Management Tools
- LDAP User and Group Management Tools
- Environment Variables
- Return Value Formats
- Common Return Codes
- The ldapuglist Tool
- The ldapugadd Tool
- The ldapugmod Tool
- The ldapugdel Tool
- The ldapcfinfo Tool
- LDAP Directory Tools
- Schema Extension Utility
- Name Service Migration Scripts
- Unsupported Contributed Tools and Scripts
- D Sample PAM Configuration File
- E Sample /etc/krb5.conf File
- F Sample /etc/pam.conf File for HP-UX 11i v1 Trusted Mode
- G Sample /etc/pam.conf File for HP-UX 11i v2 Trusted Mode
- H Sample PAM Configuration File for Security Policy Enforcement
- Glossary
- Index
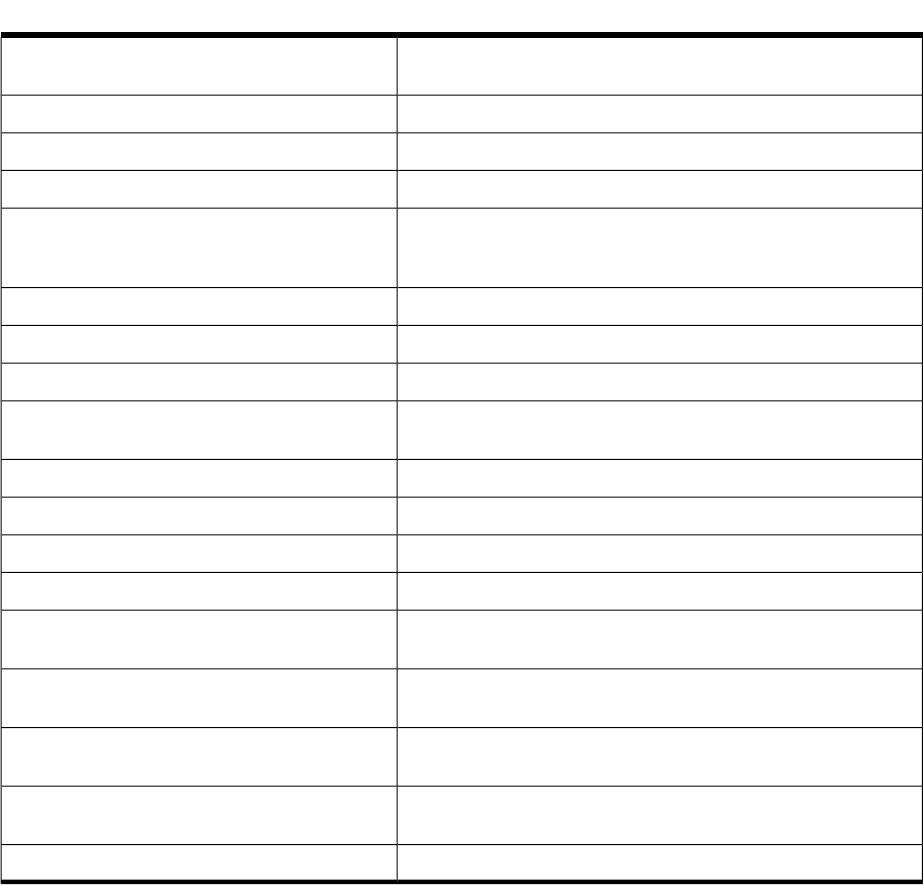
Table C-10 Return Codes for ldapcfinfo (continued)
Unable to parse following configuration line in NSS subsection
of the configuration file.
CFI_PARSE_CONFIG_FAILED
Unable to find service id for the specified service.
CFI_SEARCH_SERVICEID_FAILED
Unknown attribute for the specified service.
CFI_UNKNOWN_ATTR
Unable to verify LDAP-UX proxy credential.
CFI_VERIFY_PROXYCRED_FAILED
Unable to bind to directory server specified in the LDAP-UX
configuration profile. Please check configured host and port
numbers as well as proxy credential information if configured.
CFI_BIND_FAILED
LDAP Error 32: Configured LDAP-UX search base does not exist.
CFI_SEARCH_BASE_NOT_EXIST
Unable to verify directory server access.
CFI_VERIFY_DS_ACCESS_FAILED
LDAP-UX administrator credential file does not exist.
CFI_NOACRED
Insufficient permissions to read the LDAP-UX administrator
credential file.
CFI_NOACRED_PERM
LDAP-UX administrator credential file contains invalid credentials.
CFI_ACRED_INVALID
LDAP-UX administrator credential file valid.
CFI_ACRED_GOOD
The /etc/opt/ldapux/ldapug.conf file is missing.CFI_NO_CF_CONFIG
Unable to read the /etc/opt/ldapux/ldapug.conf file.CFI_READCONFIG
Invalid service name for the -a option. Only passwd and group
services are accepted.
CFI_INVALID_SV_FOR_REC
Invalid service name for the -D option. Only passwd and group
services are accepted.
CFI_INVALID_SV_FOR_DEF
Invalid configuration file. Missing required configuration
parameters.
CFI_UGCONF_INVALID
The specified service appears properly configured for LDAP-UX
operation.
CFI_CONFIG_SUCCESS
The specified service not configured for LDAP-UX support.
CFI_CONFIG_FAILURE
Examples
This section provides examples of using the ldapcfinfo tool:
The following command checks to see if the LDAP-UX is properly configured for the passwd
service:
cd /opt/ldapux/bin
./ldapcfinfo -t passwd
If the LDAP-UX is properly configured, below is the output of the above command:
INFO: CIF_CONFIG_SUCCESS
"passwd" service appears properly configured for LDAP-UX operation
The following command displays the attribute mapping for the gecos attribute which has been
mapped to the cn, l, and telephone attributes:
./ldapcfinfo -t passwd -m gecos
The output of the command is as follows:
gecos=cn l telephoneNumber
222 Command, Tool, Schema Extension Utility, and Migration Script Reference










