LDAP-UX Client Services B.04.15 with Microsoft Windows Active Directory Server Administrator's Guide (edition 8)
Table Of Contents
- LDAP-UX Client Services B.04.15 with Microsoft Windows Active Directory Administrator's Guide
- Table of Contents
- Preface
- 1 Introduction
- 2 Installing LDAP-UX Client Services
- Before You Begin
- Summary of Installing and Configuring LDAP-UX Client Services
- Planning Your Installation
- Installing LDAP-UX Client Services on a Client
- Configuring Active Directory for HP-UX Integration
- Step 1: Install Active Directory
- Step 2: Install SFU 2.0, 3.0 or 3.5 including Server for NIS
- Step 3: Create a Proxy User
- Step 4: Add an HP-UX Client Machine Account to Active Directory
- Step 5: Use ktpass to Create the Keytab File for the HP-UX client machine
- Step 6: Add POSIX Attributes into the Global Catalog
- Importing Name Service Data into Your Directory
- Configuring LDAP-UX Client Services
- Step 1: Run the Setup Program
- Step 2: Install the PAM Kerberos Product
- Step 3: Configure Your HP-UX Machine to Authenticate Using PAM Kerberos
- Step 4: Configure the Name Service Switch (NSS)
- Step 5: Configure the PAM Authorization Service Module (pam_authz)
- Step 6: Configure the Disable Login Flag
- Step 7: Verify LDAP-UX Client Services for Single Domain
- Step 8: Configure Subsequent Client Systems
- Configuring the LDAP-UX Client Services with SSL or TLS Support
- Downloading the Profile Periodically
- 3 Active Directory Multiple Domains
- 4 LDAP-UX Client Services with AutoFS Support
- 5 LDAP Printer Configurator Support
- 6 Dynamic Group Support
- 7 Administering LDAP-UX Client Services
- Using the LDAP-UX Client Daemon
- Integrating with Trusted Mode
- SASL GSSAPI Support
- PAM_AUTHZ Login Authorization
- Policy And Access Rules
- How Login Authorization Works
- PAM_AUTHZ Supports Security Policy Enforcement
- Policy File
- Policy Validator
- Dynamic Variable Support
- Constructing an Access Rule in pam_authz.policy
- Static List Access Rule
- Dynamic Variable Access Rule
- Security Policy Enforcement with Secure Shell (SSH) or r-commands
- Adding Additional Domain Controllers
- Adding Users, Groups, and Hosts
- User and Group Management
- Displaying the Proxy User's Distinguished Name
- Verifying the Proxy User
- Creating a New Proxy User
- Displaying the Current Profile
- Creating a New Profile
- Modifying a Profile
- Changing Which Profile a Client is Using
- Creating an /etc/krb5.keytab File
- Considering Performance Impacts
- Client Daemon Performance
- Troubleshooting
- 8 Modifying User Information
- 9 Mozilla LDAP C SDK
- A Configuration Worksheet
- B LDAP-UX Client Services Object Classes
- C Command, Tool, Schema Extension Utility, and Migration Script Reference
- LDAP-UX Client Services Components
- Client Management Tools
- LDAP User and Group Management Tools
- Environment Variables
- Return Value Formats
- Common Return Codes
- The ldapuglist Tool
- The ldapugadd Tool
- The ldapugmod Tool
- The ldapugdel Tool
- The ldapcfinfo Tool
- LDAP Directory Tools
- Schema Extension Utility
- Name Service Migration Scripts
- Unsupported Contributed Tools and Scripts
- D Sample PAM Configuration File
- E Sample /etc/krb5.conf File
- F Sample /etc/pam.conf File for HP-UX 11i v1 Trusted Mode
- G Sample /etc/pam.conf File for HP-UX 11i v2 Trusted Mode
- H Sample PAM Configuration File for Security Policy Enforcement
- Glossary
- Index
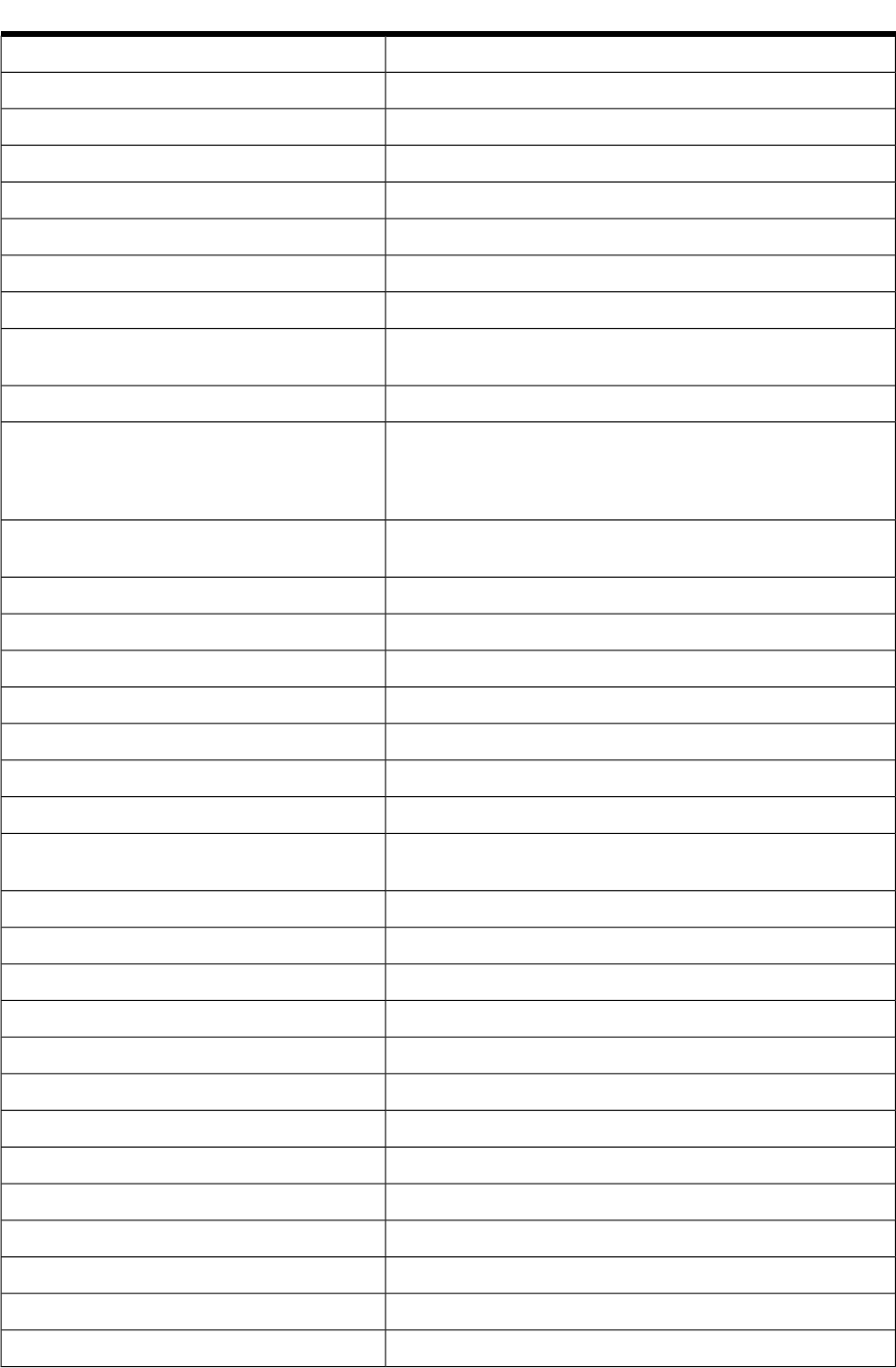
Table C-5 Common Return Codes (continued)
Failed to decrypt proxy and credential information.
GET_PROXY_DECRYPT_FAILED
There are too many modifications to perform.
MOD_LIMIT_REACHED
SSL initialization failed.
SSL_INIT_FAILED
Failed to load the specific library.
LOAD_LIB_FAILED
Failed to load the specific function.
LOAD_FUNCTION_FAILED
Unable to access specified template file.
ACCESS_TEMPLATEFILE_FAILED
Unable to read specified template file.
READ_TEMPLATEFILE_FAILED
The specified template file is missing the required directive.
MISSING_DIRECTIVE
The template file name specified in the -T <file_name> option
is invalid.
INVALID_TEMPLATENAME
Needs to configure LDAP-UX to use proxy credential level.
NEED_CONFIG_PROXY
Requires administrator credentials in order to perform privilege
user management operations. Specification of the -P option or
the LDAP_BINDDN and LDAP_BINDCRED environment variables
are required.
NEED_ADMIN_CRED
LDAP-UX proxy has been configured, but the
/etc/opt/ldapux/pcred file does not exist.
NO_PROXY_FILE
Buffer overflowed when processing a specific operation.
BUFFER_OVERFLOW
Failed to change the ownership of the files.
CHOWN_FAILED
Cannot modify the specified home directory.
CHOWN_FAILED
Failed to create the specified home directory.
HOMEDIR_CREATE_FAILED
The specified directory is not a valid directory.
INVALID_DIR
The specified home directory already exists.
HOMEDIR_EXISTS
The specified account does not exist in the directory server.
ACCOUNT_DOESNOT_EXIST
The valid type of the -t <type> option should be either passwd
or group.
COMMANDLINE_ERR
Need to specify a value for the specified option.
COMMANDLINE_ERR
User name has not been specified.
COMMANDLINE_ERR
Group name has not been specified.
COMMANDLINE_ERR
Invalid <attr>=<value> pair specified in the command line.COMMANDLINE_ERR
Entered inconsistent password.
PASSWD_INCONSISTENT
Cannot read password.
CANNOT_GET_PASSWD
Password entered is 0 length.
ZERO_LENGTH_PASSWD
The specific environment variable is not set.
ENV_VAR_NOT_SET
The input search scope must be base, one, or sub.INVALID_SEARCH_SCOPE
The specified group does not exist in the LDAP directory server.
GROUP_DOESNOT_EXIST
The specified login shell does not exist.
LOGIN_SHELL_DOESNOT_EXIST
The specified home directory does not exist.
HOMEDIR_DOESNOT_EXIST
The specified login shell is not executable.
LOGIN_SHELL_NOT_EXECUTE
LDAP User and Group Management Tools 173










