LDAP-UX Client Services B.04.15 with Microsoft Windows Active Directory Server Administrator's Guide (edition 8)
Table Of Contents
- LDAP-UX Client Services B.04.15 with Microsoft Windows Active Directory Administrator's Guide
- Table of Contents
- Preface
- 1 Introduction
- 2 Installing LDAP-UX Client Services
- Before You Begin
- Summary of Installing and Configuring LDAP-UX Client Services
- Planning Your Installation
- Installing LDAP-UX Client Services on a Client
- Configuring Active Directory for HP-UX Integration
- Step 1: Install Active Directory
- Step 2: Install SFU 2.0, 3.0 or 3.5 including Server for NIS
- Step 3: Create a Proxy User
- Step 4: Add an HP-UX Client Machine Account to Active Directory
- Step 5: Use ktpass to Create the Keytab File for the HP-UX client machine
- Step 6: Add POSIX Attributes into the Global Catalog
- Importing Name Service Data into Your Directory
- Configuring LDAP-UX Client Services
- Step 1: Run the Setup Program
- Step 2: Install the PAM Kerberos Product
- Step 3: Configure Your HP-UX Machine to Authenticate Using PAM Kerberos
- Step 4: Configure the Name Service Switch (NSS)
- Step 5: Configure the PAM Authorization Service Module (pam_authz)
- Step 6: Configure the Disable Login Flag
- Step 7: Verify LDAP-UX Client Services for Single Domain
- Step 8: Configure Subsequent Client Systems
- Configuring the LDAP-UX Client Services with SSL or TLS Support
- Downloading the Profile Periodically
- 3 Active Directory Multiple Domains
- 4 LDAP-UX Client Services with AutoFS Support
- 5 LDAP Printer Configurator Support
- 6 Dynamic Group Support
- 7 Administering LDAP-UX Client Services
- Using the LDAP-UX Client Daemon
- Integrating with Trusted Mode
- SASL GSSAPI Support
- PAM_AUTHZ Login Authorization
- Policy And Access Rules
- How Login Authorization Works
- PAM_AUTHZ Supports Security Policy Enforcement
- Policy File
- Policy Validator
- Dynamic Variable Support
- Constructing an Access Rule in pam_authz.policy
- Static List Access Rule
- Dynamic Variable Access Rule
- Security Policy Enforcement with Secure Shell (SSH) or r-commands
- Adding Additional Domain Controllers
- Adding Users, Groups, and Hosts
- User and Group Management
- Displaying the Proxy User's Distinguished Name
- Verifying the Proxy User
- Creating a New Proxy User
- Displaying the Current Profile
- Creating a New Profile
- Modifying a Profile
- Changing Which Profile a Client is Using
- Creating an /etc/krb5.keytab File
- Considering Performance Impacts
- Client Daemon Performance
- Troubleshooting
- 8 Modifying User Information
- 9 Mozilla LDAP C SDK
- A Configuration Worksheet
- B LDAP-UX Client Services Object Classes
- C Command, Tool, Schema Extension Utility, and Migration Script Reference
- LDAP-UX Client Services Components
- Client Management Tools
- LDAP User and Group Management Tools
- Environment Variables
- Return Value Formats
- Common Return Codes
- The ldapuglist Tool
- The ldapugadd Tool
- The ldapugmod Tool
- The ldapugdel Tool
- The ldapcfinfo Tool
- LDAP Directory Tools
- Schema Extension Utility
- Name Service Migration Scripts
- Unsupported Contributed Tools and Scripts
- D Sample PAM Configuration File
- E Sample /etc/krb5.conf File
- F Sample /etc/pam.conf File for HP-UX 11i v1 Trusted Mode
- G Sample /etc/pam.conf File for HP-UX 11i v2 Trusted Mode
- H Sample PAM Configuration File for Security Policy Enforcement
- Glossary
- Index
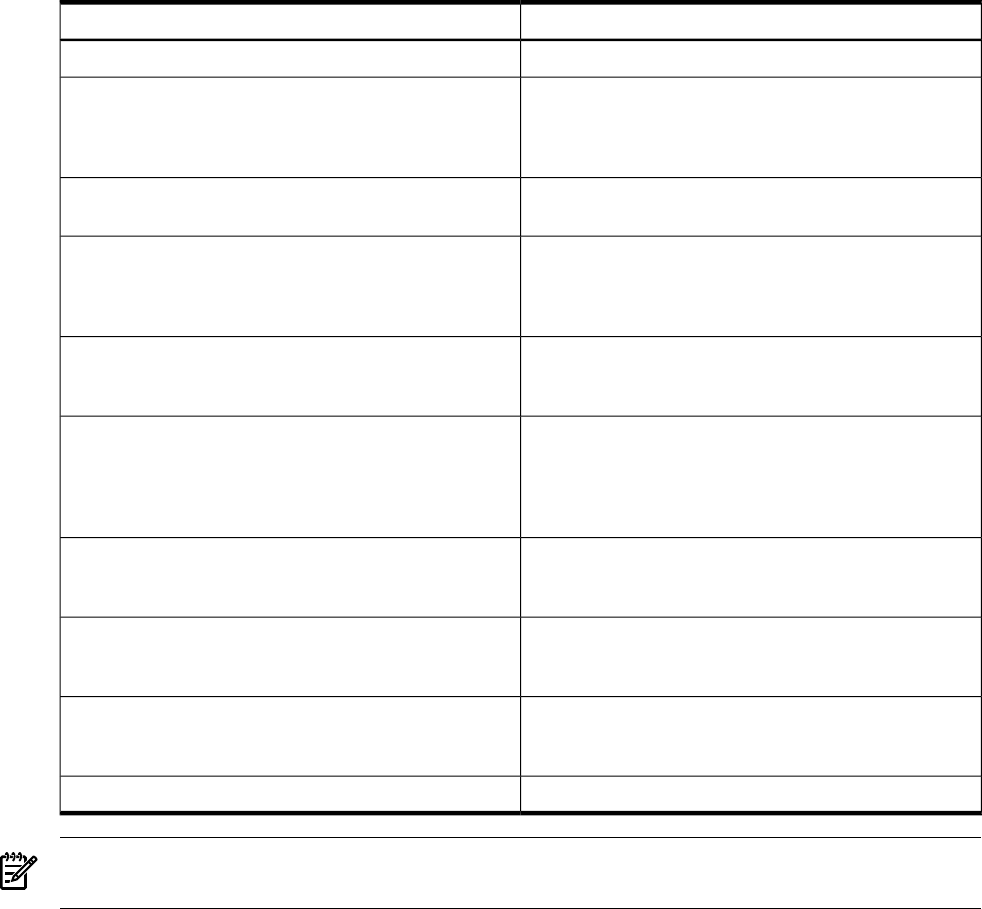
Table 9-3 Mozilla LDAP C SDK API Header Files
DescriptionHeader Files
Main LDAP functions, structures and defines./usr/include/ldap.h
Support for LDAP v3 extended operations, controls and
other server specific features. This file must be included
in source code that uses LDAP v3 extended operations or
controls.
/usr/include/ldap-extention.h
Support for creation of SSL connections. This file must be
included in source code that requires SSL connections.
/usr/include/ldap_ssl.h
Support for LDAP search preferences configuration files
(ldapsearchprefs.conf). A common method used by
applications that use the OpenLDAP API to define
organizational search preferences.
/usr/include/srchpref.h
Support for LDAP display templates. Allows applications
to convert LDAP entries into displayable text strings and
HTML.
/usr/include/disptmpl.h
Support for creating messages that follow the Basic
Encoding Rules syntax. These APIs are used when
building extended LDAP operations or controls. This file
is a support file for ldap.h and does not need to included
in source code.
/usr/include/lber.h
Contains basic LDAP defines. This file is a support file
for ldap.h and does not need to be included in source
code.
/usr/include/ldap-standard.h
Contains platform specific information for compiling on
a variety of platforms. This file is a support file for ldap.h
and does not need to be included in source code.
/usr/include/ldap-platform.h
LDAP APIs that will not be available in the future. Do
not use this header file for newly created LDAP-enabled
applications.
/opt/ldapux/include/ldap-to-be-deprecated.h
LDAP APIs that have been deprecated. Do not use./opt/ldapux/include/ldap-deprecated.h
NOTE: If you attempt to use the LDAP C SDK in your code , you only need to put in "#include
<ldap.h>" in the code and compile with the -lldap parameter to load the LDAP C SDK library.
156 Mozilla LDAP C SDK










