HP-UX Host Intrusion Detection System Version 4.3 administrator guide
Table Of Contents
- HP-UX Host Intrusion Detection System Version 4.3 administrator guide
- Table of Contents
- About This Document
- 1 Introduction
- 2 Configuring HP-UX HIDS
- 3 Getting Started with HP-UX HIDS
- 4 Using the System Manager Screen
- Starting the HP-UX HIDS System Manager
- Stopping the HP-UX HIDS System Manager
- System Manager Components
- Starting HP-UX HIDS Agents
- Getting the Status of Agent Hosts
- Resynchronizing Agent Hosts
- Activating Schedules on Agent Hosts
- Stopping Schedules on Agent Hosts
- Halting HP-UX HIDS Agents
- Accessing Other Screens
- 5 Using the Schedule Manager Screen
- The Schedule Manager
- Configuring Surveillance Schedules
- Configuring Surveillance Groups
- Configuring Detection Templates
- Setting Surveillance Schedule Timetables
- Configuring Alert Aggregation
- Configuring Monitor Failed Attempts
- Configuring Duplicate Alert Suppression
- Viewing Surveillance Schedule Details
- Predefined Surveillance Schedules and Groups
- 6 Using the Host Manager Screen
- 7 Using the Network Node Screen
- 8 Using the Preferences Screen
- A Templates and Alerts
- Alert Summary
- UNIX Regular Expressions
- Limitations
- Template Property Types
- Buffer Overflow Template
- Race Condition Template
- Modification of files/directories Template
- Changes to Log File Template
- Creation and Modification of setuid/setgid File Template
- Creation of World-Writable File Template
- Modification of Another User’s File Template
- Login/Logout Template
- Repeated Failed Logins Template
- Repeated Failed su Commands Template
- Log File Monitoring Template
- B Automated Response for Alerts
- C Tuning Schedules and Generating Alert Reports
- D The Agent Configuration File
- E The Surveillance Schedule Text File
- F Error Messages
- G Troubleshooting
- Troubleshooting
- Agent and System Manager cannot communicate with each other
- Agent complains that idds has not been enabled, yet lsdev shows /dev/idds is present
- Agent does not start on system boot
- Agent halts abnormally, leaving ids_* files and message queues
- Agent host appears to hang and/or you see message disk full
- Agent needs further troubleshooting
- Agent does not start after installation
- Agents appear to be stuck in polling status
- Agent displays error if hostname to IP mapping is not registered in name service
- Aggregated alerts targets or details field are truncated and the same aggregated alert has several entries logged in the IDS_ALERTFILE
- Alert date/time sort seems inconsistent
- Alerts are not being displayed in the alert browser
- Buffer overflow triggers false positives
- Duplicate alerts appear in System Manager
- Getting several aggregated alerts for the same process
- GUI runs out of memory after receiving around 19,000 alerts
- The idsadmin Command needs installed agent certificates
- The idsadmin Command notifies of bad certificate when pinging a remote agent
- IDS_checkInstall fails with a kmtune error
- IDS_genAdminKeys or IDS_genAgentCerts does not complete successfully
- IDS_genAdminKeys or idsgui quits early
- Large files in /var/opt/ids
- Log files are filling up
- No Agent Available
- Normal operation of an application generates heavy volume of alerts
- Reflection X rlogin produces multiple login and logout alerts
- Schedule Manager timetable screen appears to hang
- SSH does not perform a clean exit after idsagent is started
- System Manager appears to hang
- System Manager does not let you save files to specific directories
- System Manager does not start after idsgui is started
- System Manager starts with no borders or title bar in X client programs on Windows
- System Manager times out on agent functions such as Activate and Status Poll
- UNKNOWN program and arguments in certain alert messages
- Using HP-UX HIDS with IPFilter and SecureShell
- Unable to Generate Administrator Keys and Agent Certificates on PA–RISC 1.1 Systems
- Troubleshooting
- H HP Software License
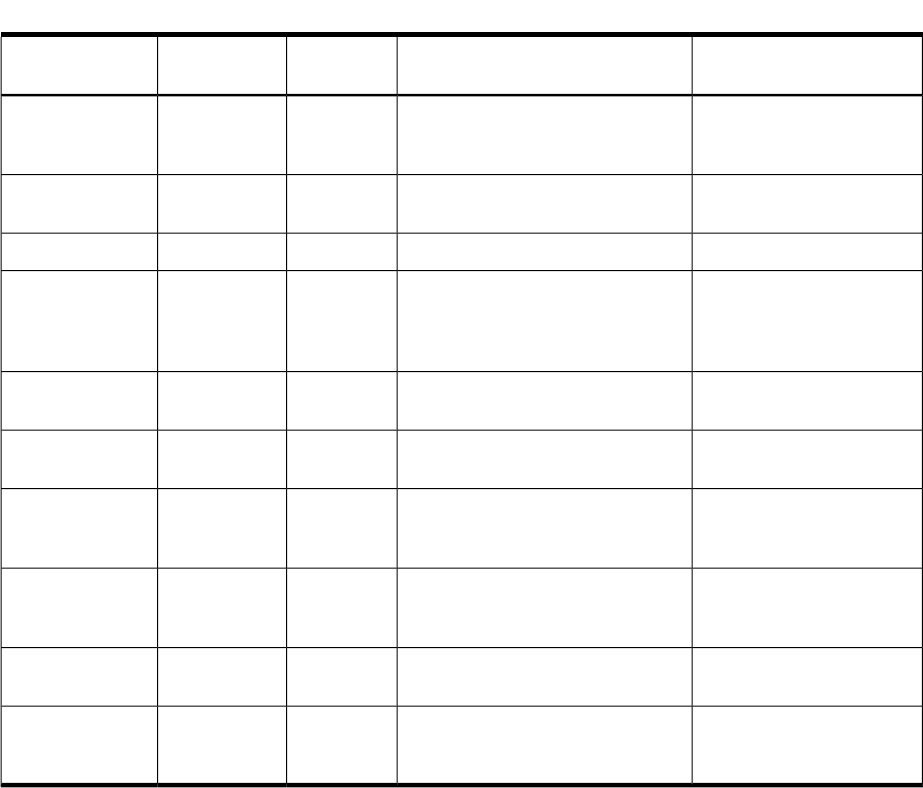
Table A-26 Failed Login Attempts Alert Properties (continued)
DescriptionAlert Value/FormatAlert Field
Type
Alert FieldResponse Program
Argument
Name or IP address of the
host from which the user
logged in or out.
<fully qualified host name>
<IP Address>
StringAttackerargv[5]
Name of the user who
logged in or out.
<username>
StringTargetargv[6]
Alert summaryFailed login attemptsStringSummaryargv[7]
Detailed alert description
More than <max_failed_login>
failed logins by user <username>
(REMOTE: <fully qualified host
name> <IP address>)
StringDetailsargv[8]
The event that triggered the
alert.
Failed login
StringEventargv[9]
Indicates a failed login alert
versus a failed su alert
1IntegerFlagargv[10]
Target login name that a
user was attempting to log
in as
<username>
StringUserargv[11]
Name of pty device
associated with failed login
attempt
<pty device name>
StringDeviceargv[12]
Name of remote host from
which login was attempted
<remote hostname>
StringHostnameargv[13]
IP address of remote host
from which login was
attempted
<A.B.C.D> for IPv4 addresses
A:B:C:D:... for IPv6 addresses
StringIP Addressargv[14]
Limitations
The Repeated Failed Logins template has the following limitations:
• The template only detects failed logins that are logged to btmp.
— The template does not detect failed secure ftp (sftp) logins because the ssh daemon logs
failed sftp logins using syslog( 3C) instead of logging them to btmps on HP–UX 11i v2
and HP-UX 11i v3.
— The template does not detect failed secure shell (ssh) logins by ssh daemons that do not
log failed ssh logins to btmp(s) on HP–UX 11i v2 and HP-UX 11i v3. To enable Secure
Shell to log failed logins and logouts to wtmp(s) or btmp(s), you must set the
permissions of the wtmp(s) or btmp(s) file to 600.
Repeated Failed su Commands Template
The vulnerability addressed by this template
The system su(1) command allows one user to assume the identity of another user by entering
that user’s password. An attacker can attempt to gain superuser (root) privileges by running the
su command and guessing the superuser password.
How this template addresses the vulnerability
The template monitors for repeated failed attempts to change user IDs. The template generates
an alert when a given number of failed change user ID attempts occurs for a specified target
user.
Repeated Failed su Commands Template 153










