HP-UX Host Intrusion Detection System Version 4.3 administrator guide
Table Of Contents
- HP-UX Host Intrusion Detection System Version 4.3 administrator guide
- Table of Contents
- About This Document
- 1 Introduction
- 2 Configuring HP-UX HIDS
- 3 Getting Started with HP-UX HIDS
- 4 Using the System Manager Screen
- Starting the HP-UX HIDS System Manager
- Stopping the HP-UX HIDS System Manager
- System Manager Components
- Starting HP-UX HIDS Agents
- Getting the Status of Agent Hosts
- Resynchronizing Agent Hosts
- Activating Schedules on Agent Hosts
- Stopping Schedules on Agent Hosts
- Halting HP-UX HIDS Agents
- Accessing Other Screens
- 5 Using the Schedule Manager Screen
- The Schedule Manager
- Configuring Surveillance Schedules
- Configuring Surveillance Groups
- Configuring Detection Templates
- Setting Surveillance Schedule Timetables
- Configuring Alert Aggregation
- Configuring Monitor Failed Attempts
- Configuring Duplicate Alert Suppression
- Viewing Surveillance Schedule Details
- Predefined Surveillance Schedules and Groups
- 6 Using the Host Manager Screen
- 7 Using the Network Node Screen
- 8 Using the Preferences Screen
- A Templates and Alerts
- Alert Summary
- UNIX Regular Expressions
- Limitations
- Template Property Types
- Buffer Overflow Template
- Race Condition Template
- Modification of files/directories Template
- Changes to Log File Template
- Creation and Modification of setuid/setgid File Template
- Creation of World-Writable File Template
- Modification of Another User’s File Template
- Login/Logout Template
- Repeated Failed Logins Template
- Repeated Failed su Commands Template
- Log File Monitoring Template
- B Automated Response for Alerts
- C Tuning Schedules and Generating Alert Reports
- D The Agent Configuration File
- E The Surveillance Schedule Text File
- F Error Messages
- G Troubleshooting
- Troubleshooting
- Agent and System Manager cannot communicate with each other
- Agent complains that idds has not been enabled, yet lsdev shows /dev/idds is present
- Agent does not start on system boot
- Agent halts abnormally, leaving ids_* files and message queues
- Agent host appears to hang and/or you see message disk full
- Agent needs further troubleshooting
- Agent does not start after installation
- Agents appear to be stuck in polling status
- Agent displays error if hostname to IP mapping is not registered in name service
- Aggregated alerts targets or details field are truncated and the same aggregated alert has several entries logged in the IDS_ALERTFILE
- Alert date/time sort seems inconsistent
- Alerts are not being displayed in the alert browser
- Buffer overflow triggers false positives
- Duplicate alerts appear in System Manager
- Getting several aggregated alerts for the same process
- GUI runs out of memory after receiving around 19,000 alerts
- The idsadmin Command needs installed agent certificates
- The idsadmin Command notifies of bad certificate when pinging a remote agent
- IDS_checkInstall fails with a kmtune error
- IDS_genAdminKeys or IDS_genAgentCerts does not complete successfully
- IDS_genAdminKeys or idsgui quits early
- Large files in /var/opt/ids
- Log files are filling up
- No Agent Available
- Normal operation of an application generates heavy volume of alerts
- Reflection X rlogin produces multiple login and logout alerts
- Schedule Manager timetable screen appears to hang
- SSH does not perform a clean exit after idsagent is started
- System Manager appears to hang
- System Manager does not let you save files to specific directories
- System Manager does not start after idsgui is started
- System Manager starts with no borders or title bar in X client programs on Windows
- System Manager times out on agent functions such as Activate and Status Poll
- UNKNOWN program and arguments in certain alert messages
- Using HP-UX HIDS with IPFilter and SecureShell
- Unable to Generate Administrator Keys and Agent Certificates on PA–RISC 1.1 Systems
- Troubleshooting
- H HP Software License
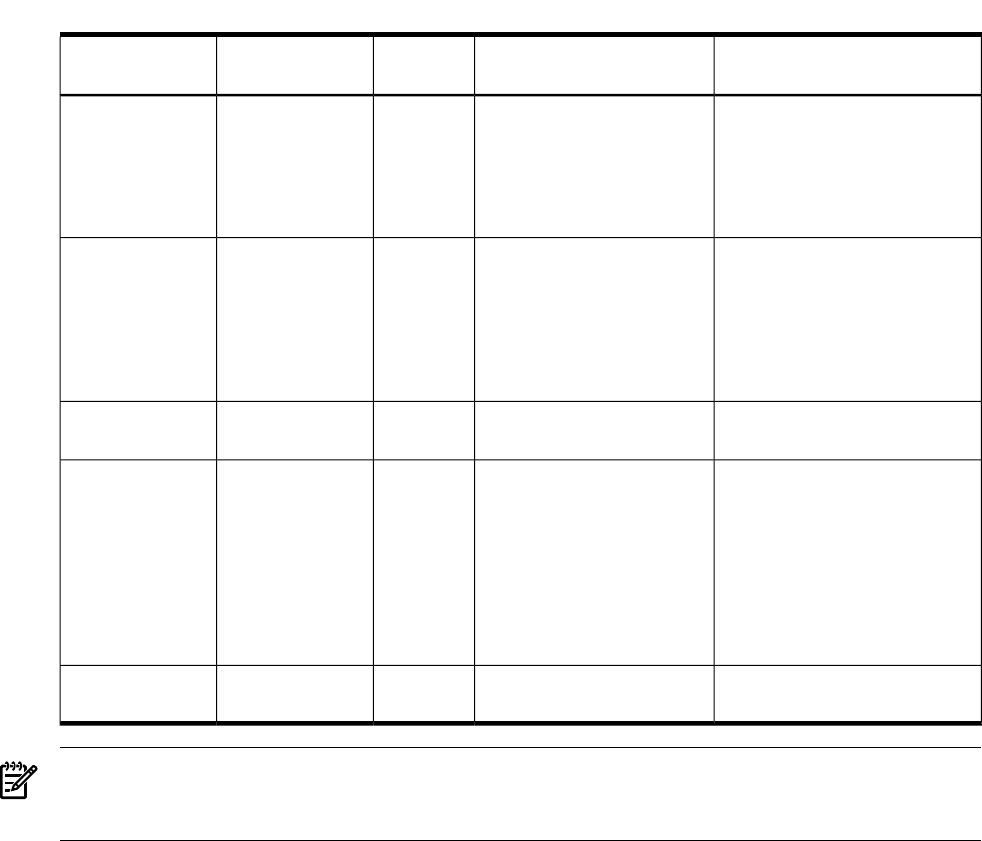
Table A-5 Argument with Nonprintable Character Alert Properties (continued)
DescriptionAlert Value/FormatAlert Field
Type
Alert FieldResponse Program
Argument
The user ID, group ID, process
ID, and parent process ID of the
process that executed a
privileged setuid program
with an argument that contains
a nonprintable character
uid=<uid>, gid=<gid>,
pid=<pid>, ppid=<ppid>
StringAttackerargv[5]
The full path name of the
setuid program the attacker
executed with an argument that
contains a nonprintable character
and the program’s type mode,
uid, gid, inode, and device
number
file=<full pathname>,
type=<type>, mode=<mode>,
uid=<uid>, gid=<gid>,
inode=<inode>,
device=<device>
StringTarget of attackargv[6]
Alert summaryPotential buffer overflow
detected
StringSummaryargv[7]
Detailed alert descriptionPotential buffer overflow
attack by process with pid
<pid> and ppid <ppid> when
executing <program>(type=
<type>, inode=<inode>,
device=<device), invoked as
follows: <argv[0]><argv[1]>
contains non-printable
characters.
StringDetailsargv[8]
The event that triggered the
alert.
nullStringEventargv[9]
NOTE: Table B-1 (page 161) in Appendix B for the definition of additional arguments, that can
be used to access specific alert information (for example, pid and ppid) without parsing the string
alert fields above.
Limitations
The Buffer Overflow template has the following limitations:
• The template does not detect whether a buffer overflow attack was successful. It only detects
that one might have been attempted.
• The template only reports exec-on-stack buffer overflow attacks on HP-UX 11i when
exec-on-stack protection is enabled.
Race Condition Template
The vulnerability addressed by this template
Some attacks use the time between a program’s check of a file and the time that the program
uses that file. The race condition is sometimes referred to as the Time-To-Check-To-Time-To-Use
(TOCTTOU) vulnerability. For instance, a mail delivery program checks to see if a file exists
before it changes ownership of the file to the intended recipient. If an attack can change the file
reference between these two steps, it can cause the program to change the ownership of an
arbitrary file.
Certain TOCTTOU attacks against privileged setuid scripts use the time between the kernel
determining that program is a privileged script and spawns an interpreter with privilege, and
the interpreter opening the script to execute it. If an attacker can change the file reference between
these two steps, it can cause the interpreter to execute an arbitrary script with privilege. An
attacker can exploit the vulnerability by repeatedly executing a privileged setuid script with
Race Condition Template 125










