HP-UX AAA Server A.08.01 administrator's guide (T1428-90072, May 2010)
Table Of Contents
- HP-UX AAA Server A.08.01 administrator’s guide
- Table of Contents
- About This Document
- Part I Introduction
- 1 Overview: The HP-UX AAA Server
- 2 Upgrading to Version A.08.01
- 3 Installing and Securing the HP-UX AAA Server
- Acquiring the HP-UX AAA Server Software
- Installing and Uninstalling the HP-UX AAA Server
- HP-UX AAA Server File Locations
- Securing the HP-UX AAA Server
- Changing the Default HP-UX AAA Server Settings
- Environment Specific Security Procedures
- Using Secure Socket Layer (SSL) for Secured Remote Server Manager Administration
- Creating a Tomcat Identity Specifically for the HP-UX AAA Server
- Running the HP-UX AAA Server on Hosts with System Hardening Software
- Running the HP-UX AAA Server as a Non-Root User
- Setting Up the HP-UX AAA Server to Start as Non-Root User After Reboot
- 4 Enabling the HP-UX AAA Server for GUI-based Administration
- Part II Configuring the HP-UX AAA Server Manager Using the Server Manager GUI
- 5 The HP-UX AAA Server Manager Interface
- 6 Managing HP-UX AAA Servers
- 7 Configuring RADIUS Clients Using the Access Devices Screen
- 8 Configuring Realms
- 9 Configuring Proxies
- 10 Configuring Users
- 11 Modifying Server Properties
- Navigating the Server Properties Screen
- DHCP Relay Properties
- DNS Updates Properties
- Message Handling Properties
- SNMP Properties
- Tunneling Properties
- Certificate Properties
- File Size Properties
- Miscellaneous Properties
- Local Users File Properties
- ProLDAP Properties
- AAA Server As A Client Properties
- Client Action Properties
- 12 Logging and Monitoring
- Overview
- Server Log Files
- Accounting Log Files
- Using Server Manager to Retrieve Accounting Logfiles
- Format of Accounting Records in the Default Merit Style
- Writing Livingston CDR Accounting Records
- Changing the Accounting Log Filename
- Changing the Accounting Log Rollover Interval
- Rolling Over the Log File and Accounting Stream and Setting the Log Level
- Part III Advanced Configuration Information
- 13 Securing LAN Access With EAP
- 14 Managing Sessions
- 15 Assigning IP Addresses
- 16 OATH Standards-Based OTP Authentication
- OTP and OATH Overview
- HP-UX AAA Server and OATH Support
- Supported OTP Functions for RADIUS Standard Password (PAP) and MS-CHAP v2
- Components Required to Configure OTP Authentication
- Configuring OTP Authentication on the HP-UX AAA Server
- OTP Authentication Configuration Flowchart
- Basic or Typical Configuration
- Advanced Configuration
- Predefined Mapping and Conversion Functions
- Sample Configuration Files
- 17 Configuring EAP-SIM and EAP-AKA Authentication Methods
- EAP-SIM
- EAP-AKA
- Fast Re-Authentication
- Pseudonym Identities
- Generating Authentication Vectors Using A3, A8, and AKA Algorithms
- 18 Configuring HP-UX AAA Server for Scalability and High-Availability
- Overview
- Scalability and High-Availability Concepts
- HP-UX AAA Server Deployment for Scalability and High-Availability
- Managing Multiple HP-UX AAA Servers For Scalability and High-Availability
- Disaster Recovery of the HP-UX AAA Server Manager
- 19 Configuring the HP-UX AAA Server for Client Functionality
- 20 Configuring the HP-UX AAA Server for Dynamic Authorization
- Dynamic Authorization Overview
- HP-UX AAA Server and Dynamic Authorization
- Processing of Dynamic Authorization Requests
- Configuring for Dynamic Authorization
- Basic Configuration
- Advanced Configuration
- Sample Configuration Files
- Part IV Integrating the HP-UX AAA Server With External Services
- 21 LDAP Authentication
- 22 SQL Access
- SQL Access Overview
- Implementing SQL Access
- Administering Users and Tokens Stored in an SQL Database
- Multi-Row Support For SQL Access
- 23 Simple Network Management Protocol (SNMP) Support
- 24 VPN Tunneling
- 25 Using DHCP
- Part V Customizing the HP-UX AAA Server
- 26 Customizing the HP-UX AAA Server Using the Finite State Machine
- 27 Customizing the HP-UX AAA Server Using Policies
- 28 Customizing the HP-UX AAA Server Using the SDK
- Part VI Troubleshooting
- 29 Troubleshooting Overview
- 30 Troubleshooting Procedures
- Troubleshooting Flowchart
- Troubleshooting the Server Manager Administration Utility
- Troubleshooting the HP-UX AAA Server
- 31 Troubleshooting Resources
- 32 Reporting Problems
- Part VII Reference
- 33 Configuration Files
- HUP Processing
- The aaa.config File
- Variables in the aaa.config File
- The strict_duplicate_check Variable
- The aatv.ProLDAP Property
- The iaaa.SNMP Property
- The log_threshold_limit and suppression_interval Variables
- The list_copy_limit Variable
- The localUsersFile.FilterType Property
- The default_users_file_cis_search Property
- The log_forwarding Variable
- The log_generated_request Variable
- The ourhostname Variable
- The packet_log Variable
- The radius_log_fmt Variable
- The reply_check Variable
- OTP Authentication-Related Configuration Items
- Dynamic Authorization-Related Configuration Items
- Variables in the aaa.config File
- The clients File
- The users File
- The dictionary File
- The las.conf File
- The vendors File
- The log.config File
- 34 Attribute-Value Pairs
- 35 MIB Objects
- 33 Configuration Files
- A Supported IETF RFCs
- B Supported Authentication Methods
- C RADIUS Data Packets
- D Header Files, Data Structures, and APIs in the HP-UX AAA Server SDK
- E Syntax of the Decision Files in Earlier Versions of the HP-UX AAA Server
- Glossary of Terms
- Index
C RADIUS Data Packets
The Access-Request and other RADIUS data packets contain a header and a set of
attribute-value (A-V) pairs, which are used by the server during the AAA transaction.
The RADIUS RFC 2865 defines how vendors can extend the protocol. Encapsulation
is the RFC defined way of extending RADIUS. Conflicts can occur when the RFC is not
followed. In those cases, the server can map the attributes to unique internal values
for processing. For a full description of RADIUS attribute-value pairs, see Chapter 34:
“Attribute-Value Pairs” (page 546).
Data Packet Format
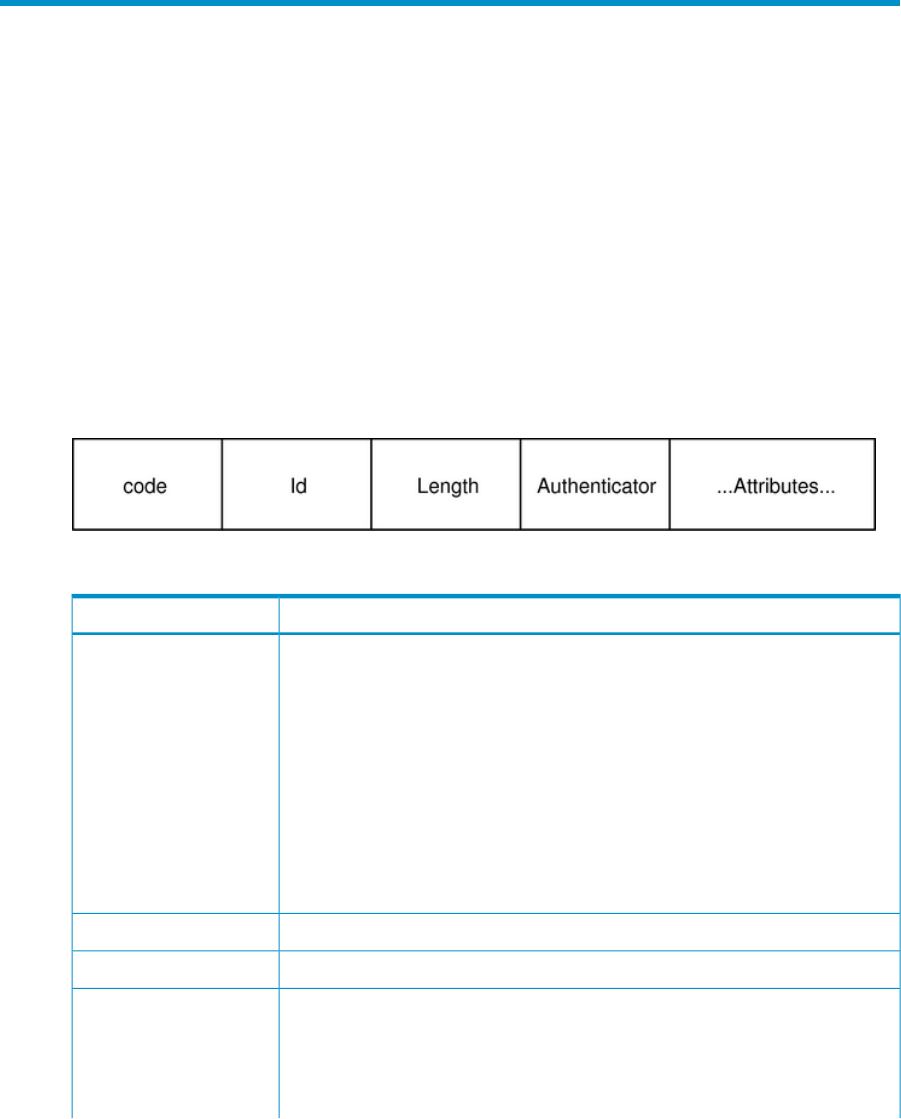
RADIUS requests and replies share a common format, see Figure C-1). These messages
are transported by UDP. By default, the server listens on UDP port 1812 for
Access-Requests and port 1813 for Accounting-Requests.
Figure C-1 RADIUS Request/Reply Message Format
Table C-1 RADIUS Request/Reply Message Format Description
DescriptionData
8-bit request/reply type
1=Access-Request
Code
2=Access-Accept
3=Access-Reject
4=Accounting-Request
5=Accounting-Response
11=Access-Challenge
40=Disconnect-Request
41=Disconnect-ACK
42=Disconnect-NAK
43=CoA-Request
44=CoA-ACK
45=CoA-NAK
8-bit message sequence number: value in reply = value in request.Id
16-bit message length, including the header beginning at Code.Length
16 octet binary vector: For Access requests, value in request is randomly
generated. Value in reply is MD5 digest of reply message data appended with
secret, using authenticator value from request.
Authenticator
For Accounting, Disconnect and CoA requests, value in request is MD5
digest of request message data appended with secret, using 16 zero octets as
Data Packet Format 577










