Concept Guide
Table Of Contents
- About this Guide
- About Instant
- Setting up a W-IAP
- Automatic Retrieval of Configuration
- Instant User Interface
- Initial Configuration Tasks
- Customizing W-IAP Settings
- Modifying the W-IAP Host Name
- Configuring Zone Settings on a W-IAP
- Specifying a Method for Obtaining IP Address
- Configuring External Antenna
- Configuring Radio Profiles for a W-IAP
- Configuring Uplink VLAN for a W-IAP
- Changing the W-IAP Installation Mode
- Changing USB Port Status
- Master Election and Virtual Controller
- Adding a W-IAP to the Network
- Removing a W-IAP from the Network
- VLAN Configuration
- IPv6 Support
- Wireless Network Profiles
- Configuring Wireless Network Profiles
- Configuring Fast Roaming for Wireless Clients
- Configuring Modulation Rates on a WLAN SSID
- Multi-User-MIMO
- Management Frame Protection
- Disabling Short Preamble for Wireless Client
- Editing Status of a WLAN SSID Profile
- Editing a WLAN SSID Profile
- Deleting a WLAN SSID Profile
- Wired Profiles
- Captive Portal for Guest Access
- Understanding Captive Portal
- Configuring a WLAN SSID for Guest Access
- Configuring Wired Profile for Guest Access
- Configuring Internal Captive Portal for Guest Network
- Configuring External Captive Portal for a Guest Network
- Configuring Facebook Login
- Configuring Guest Logon Role and Access Rules for Guest Users
- Configuring Captive Portal Roles for an SSID
- Configuring Walled Garden Access
- Authentication and User Management
- Managing W-IAP Users
- Supported Authentication Methods
- Supported EAP Authentication Frameworks
- Configuring Authentication Servers
- Understanding Encryption Types
- Configuring Authentication Survivability
- Configuring 802.1X Authentication for a Network Profile
- Enabling 802.1X Supplicant Support
- Configuring MAC Authentication for a Network Profile
- Configuring MAC Authentication with 802.1X Authentication
- Configuring MAC Authentication with Captive Portal Authentication
- Configuring WISPr Authentication
- Blacklisting Clients
- Uploading Certificates
- Roles and Policies
- DHCP Configuration
- Configuring Time-Based Services
- Dynamic DNS Registration
- VPN Configuration
- IAP-VPN Deployment
- Adaptive Radio Management
- Deep Packet Inspection and Application Visibility
- Voice and Video
- Services
- Configuring AirGroup
- Configuring a W-IAP for RTLS Support
- Configuring a W-IAP for Analytics and Location Engine Support
- Managing BLE Beacons
- Clarity Live
- Configuring OpenDNS Credentials
- Integrating a W-IAP with Palo Alto Networks Firewall
- Integrating a W-IAP with an XML API Interface
- CALEA Integration and Lawful Intercept Compliance
- Cluster Security
- W-IAP Management and Monitoring
- Uplink Configuration
- Intrusion Detection
- Mesh W-IAP Configuration
- Mobility and Client Management
- Spectrum Monitor
- W-IAP Maintenance
- Monitoring Devices and Logs
- Hotspot Profiles
- ClearPass Guest Setup
- IAP-VPN Deployment Scenarios
- Acronyms and Abbreviations
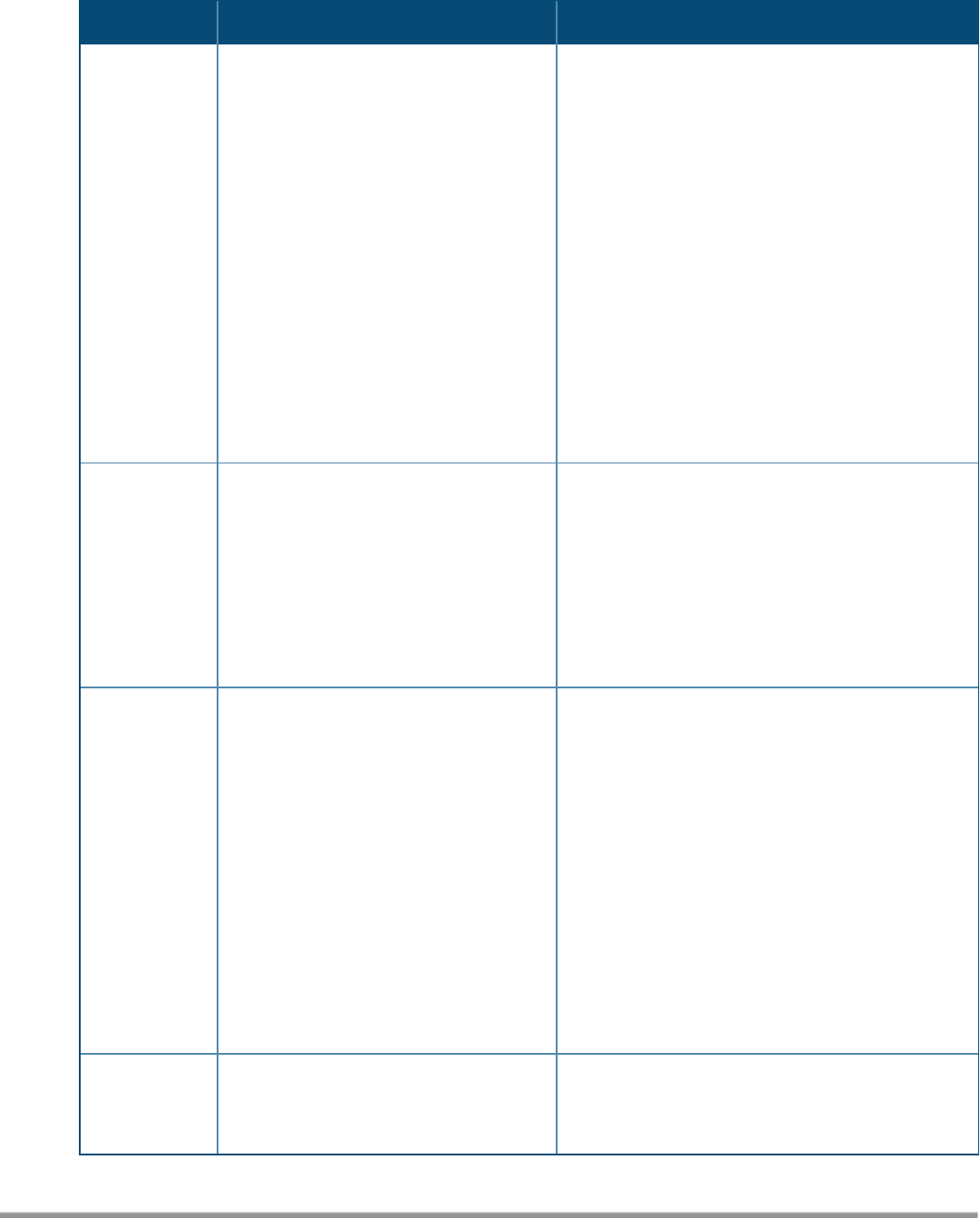
The following table describes the graphs displayed in the Access Point view:
Graph Name W-IAP Description Monitoring Procedure
Neighboring
W-IAPs
The Neighboring W-IAPs graph shows the
number of W-IAPs detected by the
selected W-IAP:
l Valid W-IAPs: A W-IAP that is part of
the enterprise providing WLAN
service.
l Interfering W-IAPs: A W-IAP that is
seen in the RF environment but is not
connected to the network.
l Rogue W-IAPs: An unauthorized W-IAP
that is plugged into the wired side of
the network.
To see the number of different types of
neighboring W-IAPs for the last 15
minutes, move the cursor over the
respective graph lines.
To check the neighboring W-IAPs detected by the W-
IAP for the last 15 minutes:
1. Log in to the Instant UI. The Virtual Controller
view is displayed. This is the default view.
2. On the Access Points tab, click the W-IAP for
which you want to monitor the client association.
3. Study the Neighboring W-IAPs graph in the
Overview section. For example, the graph shows
that 148 interfering W-IAPs are detected by the
W-IAP at 12:04 hours.
CPU Utilization The CPU Utilization graph displays the
utilization of CPU for the selected W-IAP.
To see the CPU utilization of the W-IAP,
move the cursor over the graph line.
To check the CPU utilization of the W-IAP for the last
15 minutes:
1. Log in to the Instant UI. The Virtual Controller
view is displayed. This is the default view.
2. On the Access Points tab, click the W-IAP for
which you want to monitor the client association.
3. Study the CPU Utilization graph in the Overview
pane. For example, the graph shows that the CPU
utilization of the W-IAP is 30% at 12:09 hours.
Neighboring
Clients
The Neighboring Clients graph shows the
number of clients not connected to the
selected W-IAP, but heard by it.
l Any client that successfully
authenticates with a valid W-IAP and
passes encrypted traffic is classified
as a valid client.
l Interfering: A client associated to any
W-IAP and is not valid is classified as
an interfering client.
To see the number of different types of
neighboring clients for the last 15
minutes, move the cursor over the
respective graph lines.
To check the neighboring clients detected by the W-
IAP for the last 15 minutes,
1. Log in to the Instant UI. The Virtual Controller
view is displayed. This is the default view.
2. On the Access Points tab, click the W-IAP for
which you want to monitor the client association.
3. Study the Neighboring Clients graph in the
Overview pane. For example, the graph shows
that 20 interfering clients were detected by the
W-IAP at 12:15 hours.
Memory free
(MB)
The Memory free graph displays the
memory availability of the W-IAP in MB.
To check the free memory of the W-IAP for the last
15 minutes:
1. Log in to the Instant UI. The Virtual Controller
Table 14: Access Point View—Usage Trends and Monitoring Procedures
Dell Networking W-Series Instant 6.5.1.0-4.3.1.0 | User Guide Instant User Interface | 46










