Concept Guide
Table Of Contents
- About this Guide
- About Instant
- Setting up a W-IAP
- Automatic Retrieval of Configuration
- Instant User Interface
- Initial Configuration Tasks
- Customizing W-IAP Settings
- Modifying the W-IAP Host Name
- Configuring Zone Settings on a W-IAP
- Specifying a Method for Obtaining IP Address
- Configuring External Antenna
- Configuring Radio Profiles for a W-IAP
- Configuring Uplink VLAN for a W-IAP
- Changing the W-IAP Installation Mode
- Changing USB Port Status
- Master Election and Virtual Controller
- Adding a W-IAP to the Network
- Removing a W-IAP from the Network
- VLAN Configuration
- IPv6 Support
- Wireless Network Profiles
- Configuring Wireless Network Profiles
- Configuring Fast Roaming for Wireless Clients
- Configuring Modulation Rates on a WLAN SSID
- Multi-User-MIMO
- Management Frame Protection
- Disabling Short Preamble for Wireless Client
- Editing Status of a WLAN SSID Profile
- Editing a WLAN SSID Profile
- Deleting a WLAN SSID Profile
- Wired Profiles
- Captive Portal for Guest Access
- Understanding Captive Portal
- Configuring a WLAN SSID for Guest Access
- Configuring Wired Profile for Guest Access
- Configuring Internal Captive Portal for Guest Network
- Configuring External Captive Portal for a Guest Network
- Configuring Facebook Login
- Configuring Guest Logon Role and Access Rules for Guest Users
- Configuring Captive Portal Roles for an SSID
- Configuring Walled Garden Access
- Authentication and User Management
- Managing W-IAP Users
- Supported Authentication Methods
- Supported EAP Authentication Frameworks
- Configuring Authentication Servers
- Understanding Encryption Types
- Configuring Authentication Survivability
- Configuring 802.1X Authentication for a Network Profile
- Enabling 802.1X Supplicant Support
- Configuring MAC Authentication for a Network Profile
- Configuring MAC Authentication with 802.1X Authentication
- Configuring MAC Authentication with Captive Portal Authentication
- Configuring WISPr Authentication
- Blacklisting Clients
- Uploading Certificates
- Roles and Policies
- DHCP Configuration
- Configuring Time-Based Services
- Dynamic DNS Registration
- VPN Configuration
- IAP-VPN Deployment
- Adaptive Radio Management
- Deep Packet Inspection and Application Visibility
- Voice and Video
- Services
- Configuring AirGroup
- Configuring a W-IAP for RTLS Support
- Configuring a W-IAP for Analytics and Location Engine Support
- Managing BLE Beacons
- Clarity Live
- Configuring OpenDNS Credentials
- Integrating a W-IAP with Palo Alto Networks Firewall
- Integrating a W-IAP with an XML API Interface
- CALEA Integration and Lawful Intercept Compliance
- Cluster Security
- W-IAP Management and Monitoring
- Uplink Configuration
- Intrusion Detection
- Mesh W-IAP Configuration
- Mobility and Client Management
- Spectrum Monitor
- W-IAP Maintenance
- Monitoring Devices and Logs
- Hotspot Profiles
- ClearPass Guest Setup
- IAP-VPN Deployment Scenarios
- Acronyms and Abbreviations
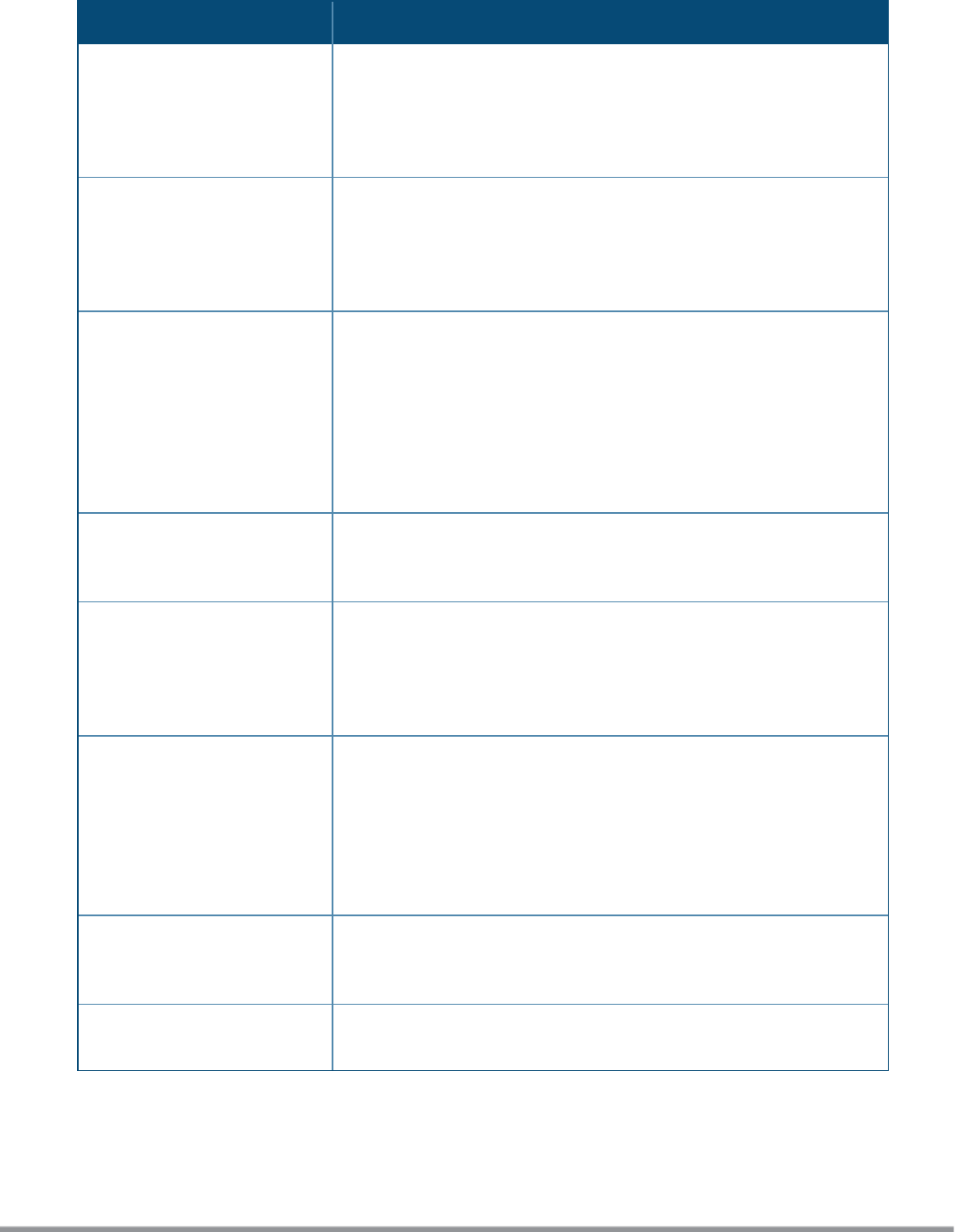
Term Definition
W-CDMA Officially known as IMT-2000 direct spread; ITU standard derived from
Code-Division Multiple Access (CDMA). Wideband code-division multiple
access (W-CDMA) is a third-generation (3G) mobile wireless technology
that promises much higher data speeds to mobile and portable wireless
devices than commonly offered in today's market.
Wi-Fi A term for certain types of WLANs. Wi-Fi can apply to products that use
any 802.11 standard. Wi-Fi has gained acceptance in many businesses,
agencies, schools, and homes as an alternative to a wired LAN. Many
airports, hotels, and fast-food facilities offer public access to Wi-Fi
networks.
WEP Wired equivalent privacy (WEP) is a security protocol specified in
802.11b, designed to provide a WLAN with a level of security and privacy
comparable to what is usually expected of a wired LAN. Data encryption
protects the vulnerable wireless link between clients and access points;
once this measure has been taken, other typical LAN security
mechanisms such as password protection, end-to-end encryption,
virtual private networks (VPNs), and authentication can be put in place to
ensure privacy.
wireless Describes telecommunications in which electromagnetic waves (rather
than some form of wire) carry the signal over part or all of the
communication path.
wireless network In a Wireless LAN (WLAN), laptops, desktops, PDAs, and other computer
peripherals are connected to each other without any network cables.
These network elements or clients use radio signals to communicate
with each other. Wireless networks are set up based on the IEEE 802.11
standards.
WISP Wireless ISP (WISP) refers to an internet service provider (ISP) that
allows subscribers to connect to a server at designated hot spots
(access points) using a wireless connection such as Wi-Fi. This type of
ISP offers broadband service and allows subscriber computers, called
stations, to access the Internet and the web from anywhere within the
zone of coverage provided by the server antenna, usually a region with
a radius of several kilometers.
wireless service provider A company that offers transmission services to users of wireless
devices through radio frequency (RF) signals rather than through end-to-
end wire communication.
WLAN Wireless local area network (WLAN) is a local area network (LAN) that
the users access through a wireless connection.
Table 88: List of Terms
Dell Networking W-Series Instant 6.5.1.0-4.3.1.0 | User Guide IAP-VPN Deployment Scenarios | 415










